Here's a question that should keep every CISO up at night: if a breach happened right now, how quickly could you tell your board exactly what the compromised account could access, across every application, API, and AI agent in your environment?
If the honest answer is "I'd need to check with three teams and read some code," you're not alone. But that delay is no longer just an operational inconvenience. It's a career-level risk.
The global average cost of a data breach hit $4.88 million in 2024, according to IBM's Cost of a Data Breach Report-the highest ever recorded. Breaches resolved in under 200 days cost roughly $3.87 million, while those exceeding 200 days climbed to $5.01 million.
The math is straightforward: every day your incident response team spends piecing together access permissions from fragmented systems directly inflates the financial and regulatory damage. And under SEC disclosure rules requiring material incident reporting within four business days, the clock doesn't wait for you to untangle your authorization spaghetti.
This is why centralized authorization governance isn't a nice-to-have infrastructure project. It's the difference between an incident response that protects the organization and one that ends with a CISO updating their LinkedIn.
The authorization visibility problem most security leaders inherit
Most enterprises have an authorization problem they can't fully see. Access control logic is scattered across application code, API gateways, feature flags, and ad-hoc checks added during previous incidents and never revisited. Each individual check might make sense in isolation, but collectively they create a system that no one can reason about end-to-end.
Ask a straightforward question-"Who can approve a payment over $50,000 in the EMEA region right now?"-and the answer is rarely a query or a report. It's usually a Slack thread, a diagram someone last updated six months ago, and a lot of caveats.
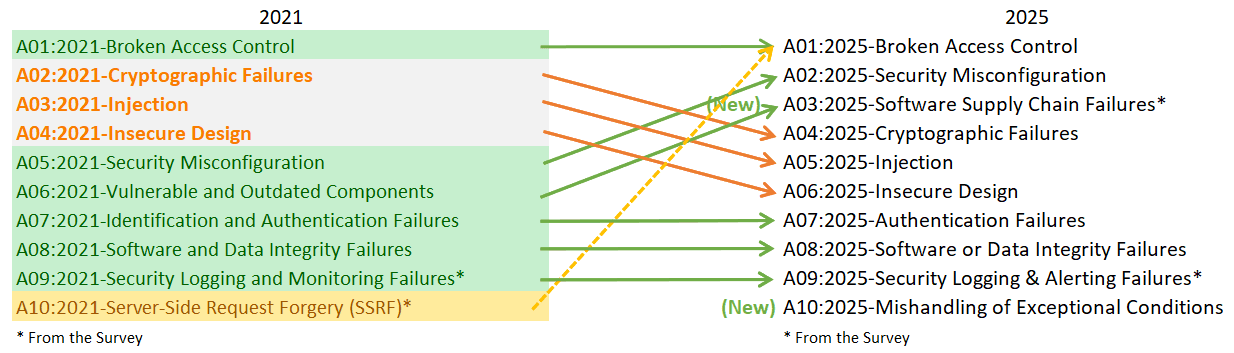
This isn't hypothetical. Broken Access Control has held the #1 spot in the OWASP Top 10 for two consecutive cycles, with the 2025 update confirming its dominance. OWASP's analysis found that 100% of applications tested had some form of broken access control. Not "most." All of them.
The root cause is architectural, not behavioral. When authorization logic is hardcoded into individual applications, security teams lose centralized visibility. From working with hundreds of security teams, talking to industry experts, and attending events like Gartner IAM, Identiverse, and EIC, we see the same pattern over and over: custom, homegrown authorization tools are the single biggest source of IAM technical debt. Static role-based tools manage access at provisioning time but lack dynamic, real-time authorization controls. Coarse-grained access management gives you a starting point, but it doesn't deliver the fine-grained, context-aware decisions that modern environments demand.
For CISOs, this fragmentation creates a specific and personal risk: when an incident occurs, you can't quickly answer the questions that regulators, boards, and legal teams will ask. Not because the information doesn't exist, but because it's buried across dozens of systems with no single source of truth.
Why incident response stalls without centralized access control
Incident response, at its core, is a race against time. The average breach lifecycle dropped to 241 days in 2025 - the fastest on record - but that's still over eight months from detection to containment. Organizations using AI-powered detection systems identify breaches 80 days faster and save $1.9 million compared to manual detection methods. But the authorization layer remains a consistent bottleneck.
When a breach happens, the incident response team needs to answer three critical questions immediately: What could this compromised identity access? What did it actually access? And how do we revoke that access without breaking everything else?
In a decentralized authorization environment, answering even the first question requires manually tracing permissions through application code, configuration files, and identity provider settings-often across different teams with different tooling and different documentation standards. The Verizon 2025 DBIR reports that stolen credentials were involved in 53% of breaches, and privilege misuse appeared in 12%. When credentials are compromised, the blast radius is determined entirely by what those credentials authorize. If you can't map that blast radius in minutes, your incident response is flying blind.
Centralized authorization governance changes this equation fundamentally. When every access decision-who, what resource, what action, allow or deny, with full context-flows through a single policy decision point, your security team can query the authorization layer directly. During an incident, instead of reconstructing what should have happened, you're inspecting evidence of what actually did happen. Logs are complete. Context is present. Decision rationale is explicit, not buried in code paths and configuration.
The AI agent dimension: A new authorization surface you can't ignore
If fragmented authorization for human users is a known problem, the arrival of AI agents has turned it into an urgent one. Across the IAM industry-from conferences like Gartner IAM EMEA, Identiverse, and EIC, to conversations with our own customers-the shift is unmistakable. AI agents have moved from "interesting demo" to board-level initiative. Enterprise AI agent adoption jumped from 11% in Q1 2025 to 42% by Q3 2025, with 88% of organizations using or planning to use AI agents. Another 34% of banks and insurers plan deployments within 12 months.
And here's the pattern that should concern every security leader: the board has bought into AI, budget is flowing, agents are being built or bought-and the identity team found out somewhere between "proof of concept" and "we're going live next month." The work to figure out who these agents are, what they can access, and how to govern delegation chains has landed on teams already stretched thin. Meanwhile, AI-borne threats are up 200% year-over-year, and 1 in 6 breaches in 2025 involved AI-driven attacks.
The consensus across the industry is as follows: current IAM controls are not built for AI agents. The authorization requirements for agents-fine-grained access control, context-aware decisions, delegation of authority with human-in-the-loop flows, and rich authorization requests, all point toward policy-based, attribute-driven authorization rather than static role assignments.
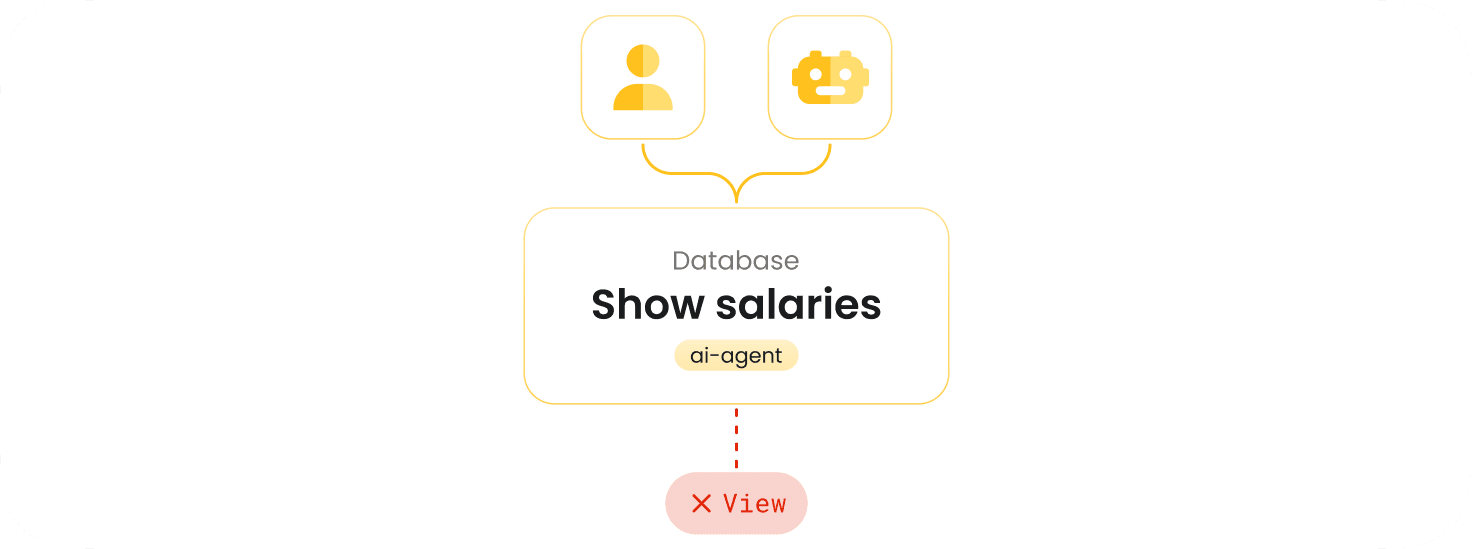
For incident response specifically, AI agents introduce a new threat vector: the Confused Deputy Problem, where an agent can be manipulated into using elevated privileges on behalf of a less-privileged caller. Without centralized authorization that validates the full request chain-user to orchestrator to agent to tool-at each hop, a compromised agent becomes an unlimited lateral movement opportunity. Industry best practice now calls for treating MCP servers as APIs, applying Zero Trust patterns, and implementing authorization at the MCP server side using a PDP/PEP in-line proxy pattern. Without centralized governance, you simply cannot do this.
Industry analysts predict that over 50% of AI initiatives will stall due to unresolved agentic identity challenges through 2028. If your authorization layer can't answer "What can this AI agent access right now?" in seconds during an incident, you have a problem that will only get worse as agent adoption accelerates.
What "centralized" actually means: Architecture, not just tooling
Centralized authorization governance doesn't mean a single monolithic access control system. It means a specific architectural pattern recognized across the IAM industry as the canonical Authorization Management Platform (AMP) design: centralized policy administration with decentralized enforcement.
In practice, this means your authorization policies are authored and managed in one place, version-controlled, testable, auditable-while enforcement happens wherever the access decision needs to be made: at your API gateway, in your application code, in your service mesh, or between an AI agent and its tools. A Policy Decision Point (PDP) evaluates context-rich requests and returns deterministic decisions. Policy Enforcement Points (PEPs) sit at each access boundary and query the PDP.
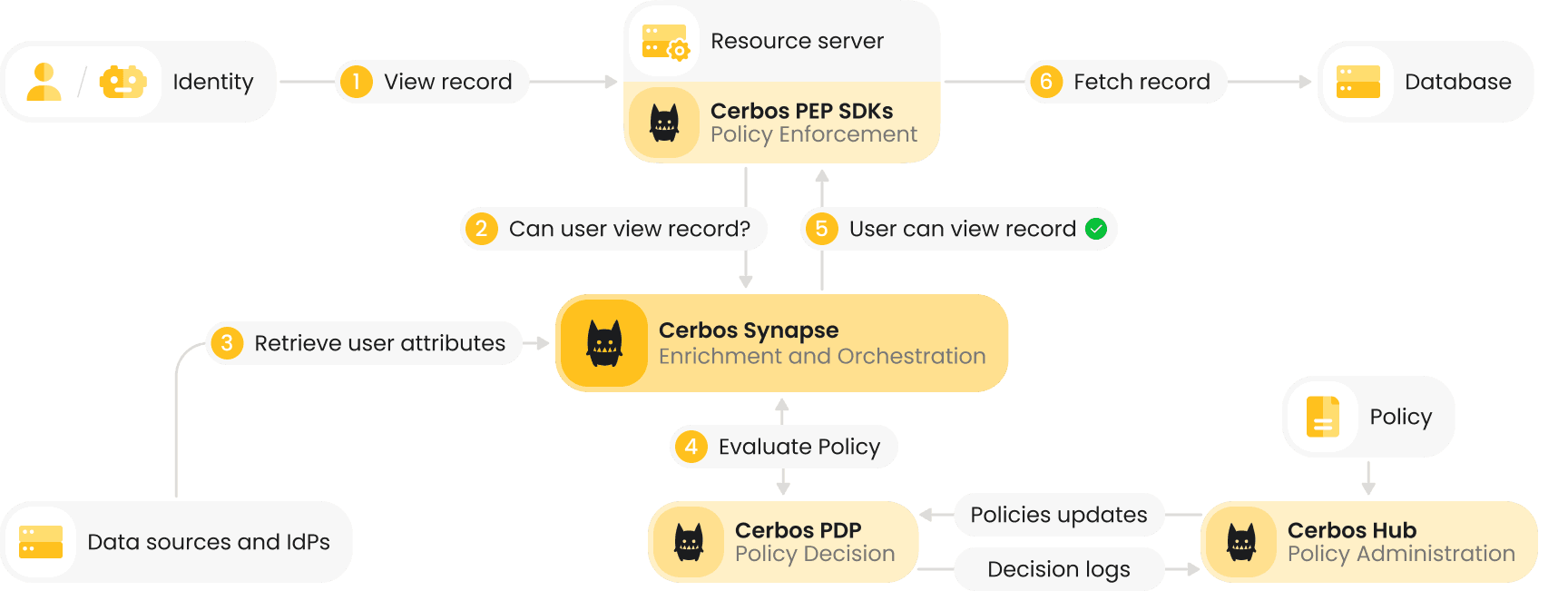
This pattern directly addresses the incident response problem. Because every decision flows through the PDP with full context-the principal, the resource, the action, the environmental conditions-you get a complete, queryable audit trail automatically. During an incident, you can ask "Show me every decision made for this identity in the last 48 hours" and get an immediate, authoritative answer. No Slack threads. No code archaeology. No guesswork.
Policy-as-code is a key enabler here. When policies are defined in a structured, version-controlled format rather than scattered across application code, you gain several incident response advantages: every policy change is tracked with full version history, you can test policies before deployment, you can diff any two versions to understand exactly what changed, and you can roll back instantly if a policy change causes unexpected behavior.
The personal liability equation CISOs can't afford to ignore
Here's where this conversation gets personal. CISOs in 2025 face an accountability landscape that has fundamentally shifted. The SEC now requires public companies to disclose material cybersecurity incidents within four business days and outline risk oversight processes in annual filings. The DOJ and international regulators are targeting executives who omit or distort cyber risk information. Individual CISOs have faced scrutiny, fines, and even criminal charges for cybersecurity failures.
Research into how CISOs actually make purchasing decisions confirms what most security leaders already know: 76% of vendor decisions come down to personal risk mitigation, not product features. The real question behind every technology decision is: "If this goes wrong, can I defend this choice to my CEO and Board?"
Centralized authorization governance gives you a defensible answer. When your authorization layer produces a complete audit trail for every access decision, you can demonstrate to regulators, boards, and auditors that you had systematic controls in place. You can prove what was enforced, not just what was intended. You can show exactly when a policy was in effect, what context was evaluated, and why a specific decision was made.
Conversely, when authorization logic is fragmented across fifty applications with no unified audit trail, defending your security posture during a regulatory inquiry becomes extraordinarily difficult. You may have had good policies in every individual system, but if you can't demonstrate centralized governance and complete evidence, the narrative you're defending is "we hoped everything was working as intended" rather than "we know exactly what happened and can prove it."
For GDPR alone, cumulative fines have exceeded €6.7 billion as of January 2026. NIS2, DORA, SOX, PCI DSS, and sector-specific regulations all mandate access controls and audit trails. The cost of poor regulatory compliance averages roughly $4.62 million per incident, according to IBM. Centralized authorization doesn't just reduce incident response time-it's the evidence base that protects your career.
Evaluating your options: Build, buy, or consolidate
If you've reached the conclusion that your authorization layer needs fixing, the next question is how. Most security leaders evaluate three approaches:
Fix fragmentation yourself. This means assigning engineering teams to audit, consolidate, and rebuild authorization logic across your application portfolio. It's the most expensive option in practice. From what we've seen working with security teams across industries, DIY authorization carries five consistent risks: developer costs, exploitable bugs, regulatory gaps, lack of community support, and slower time to market. Engineering leaders who've been through this process report costs in the seven figures, and you're still maintaining a custom system that no external community is improving.
Buy another point tool. You might add an authorization layer on top of your existing IAM stack. The risk here is adding another silo to an already fragmented environment. The industry guidance is clear: stop acquiring tools that are not interoperable. Organizations consistently report positive ROI from addressing IAM technical debt rather than adding to it.
Consolidate with a purpose-built authorization platform. This is the approach that aligns with the AMP architecture pattern: a dedicated authorization layer with centralized policy administration, decentralized enforcement, open standards support, and built-in audit capabilities.
Cerbos is an enterprise-grade authorization management platform built to secure access across complex, distributed environments, SaaS products, and regulated systems. It externalizes authorization logic from application code, making access control consistent and centrally managed across all your services. Designed for Zero Trust architectures and AI-driven systems, Cerbos provides continuous, policy-based authorization that scales from local deployments to global production systems.
Cerbos' authorization system consists of four connected components working together: the open-source Policy Decision Point (PDP), which is the authorization engine evaluating access control logic and returning allow or deny decisions-stateless, lightweight, and capable of handling millions of checks per second; Enforcement Point SDKs that enforce decisions directly within your applications and APIs; Cerbos Hub, the policy administration point for authoring, testing, deploying, and auditing policies at scale; and finally Cerbos Synapse, the latest component that gathers identity, resource, and relationship data from your existing systems - identity providers, databases, graph databases, internal APIs - and delivers complete context to the policy engine before every authorization decision.
It supports multiple access control models including RBAC, ABAC, and PBAC, giving engineering and security teams flexibility to model permissions the way their business needs them. Every access decision is recorded with detailed audit logs - who, what resource, what action, the decision, the policy version, the timestamp - ensuring every access decision meets your security and compliance requirements.
What matters for your incident response capability is whether the solution gives you a single source of truth for authorization decisions with complete, queryable audit logs. Can you trace every permission decision back to a specific policy version with full context? Can you answer "What could this identity access at 2:47 AM on Tuesday?" in seconds rather than hours? Can you revoke access patterns instantly without deploying application code? These are the capabilities that compress your incident response timeline from weeks to hours.
For a full breakdown of the build vs buy question, refer to this blog.
A practical starting point
You don't need to overhaul your entire authorization architecture overnight. Start with the assessment most industry frameworks recommend: inventory all authorization logic across your application portfolio. Identify where access decisions are made, by what mechanism, and whether they're auditable. If custom homegrown tools top your list of IAM technical debt-as they do for most organizations-that's your starting point.
From there, evaluate whether you can externalize authorization for your highest-risk applications first, establish centralized policy governance, and build the audit capability your incident response team needs. An iterative approach works best: deploy required features first, expand over time. The organizations shipping AI agents faster are the ones that built their authorization layer first. The ones stalling are trying to retrofit it after the fact.
The question isn't whether your organization needs centralized authorization governance. The data-on breach costs, incident timelines, regulatory enforcement, and AI adoption-has answered that. The question is whether you'll build that capability proactively or discover the gap during an incident, when your board, your regulators, and your career are all watching.
Ready to see what centralized authorization governance looks like in practice?
Cerbos provides the authorization infrastructure security leaders need: centralized policy control, real-time audit logs, and Zero Trust enforcement across applications, APIs, and AI systems. With an open-source core and enterprise management plane, it fits your existing IAM stack without adding another silo.
FAQ
Tagged in