Cerbos Synapse
Give every authorization decision the context it needs
Assemble identity, resource, and relationship context from your IdPs, databases, and APIs, and connect enforcement points through the protocols they already use for consistent authorization decisions

Rob Crowe, Principal Engineer, Utility Warehouse
“We rely on Cerbos to make authorization decisions across the whole mesh - millions of times a day.”
Unified authorization context
Real-time context from your data fabric
Fetch identity, resource, relationship data at decision time for true zero-trust authorization, without custom middleware or PEP code.
One platform for authorization management
End-to-end authorization across applications, infrastructure, and AI systems with a unified policy engine, data layer, and control plane.
Authorization management
Cerbos Hub
Policy Administration Point
Cerbos Hub is the control plane for policy authoring, testing, versioning, distribution, and audit visibility. Hub provides end-to-end policy management out of the box.
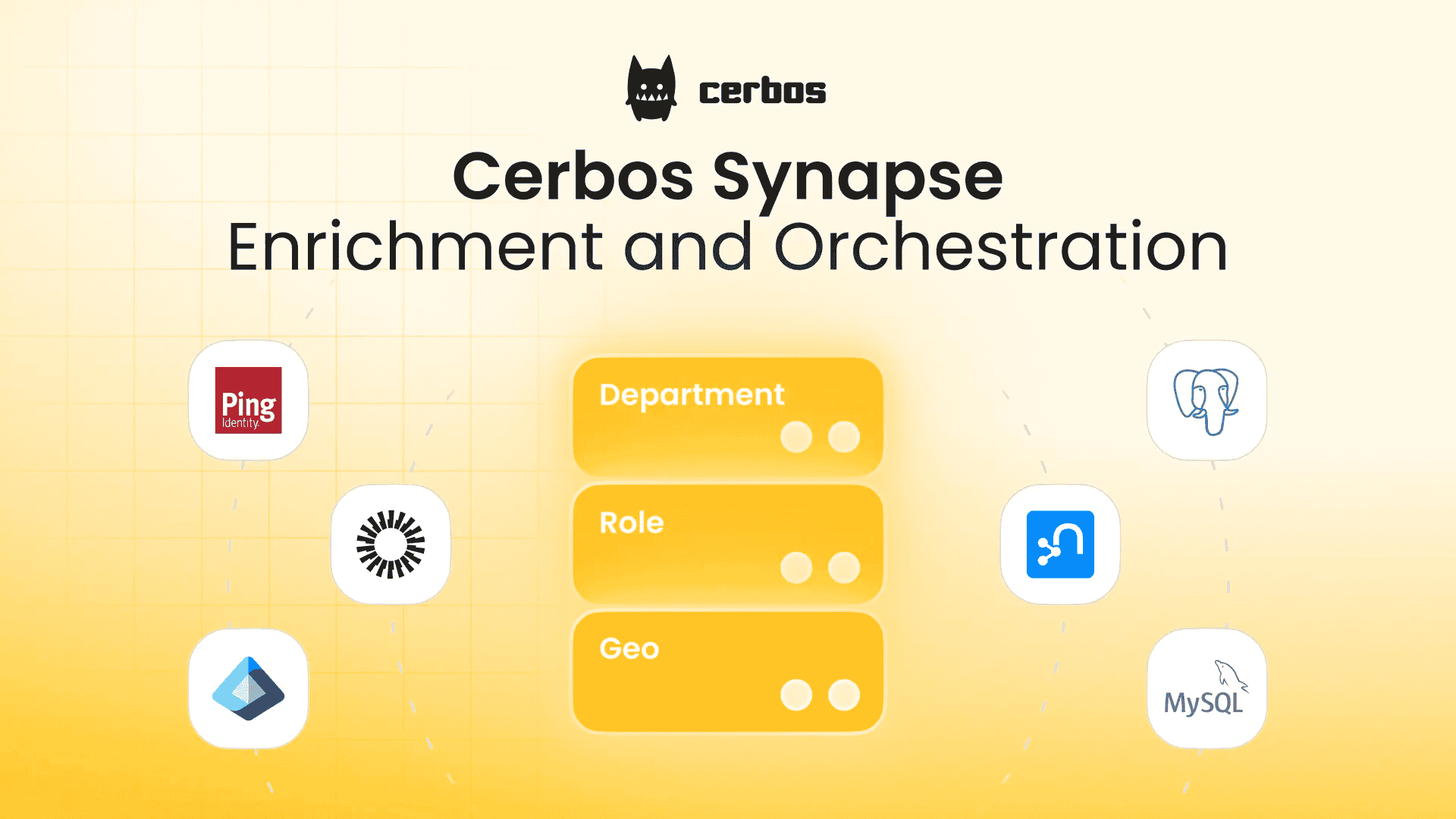
Data and Integration
Cerbos Synapse
Enrichment and Orchestration
Synapse fetches identity, resource, and relationship data from external systems to enrich authorization requests, and translates infrastructure protocols into Cerbos policy checks.
4.4k
< 1 ms decision time
Cerbos PDP
Policy Decision Point
PDP is an open source authorization engine that evaluates requests against policies and returns access decisions. It's stateless, high-performance, and built to scale horizontally.
Native SDKs
Cerbos PEP SDK
Policy Enforcement Point
Cerbos PEPs are language-native client libraries that connect applications directly to PDPs to enforce real-time access decisions, with SDKs available for all major languages.
Authorization across every system and use case
AI authorization
Enterprise app authorization
Authorization software that scales with your business
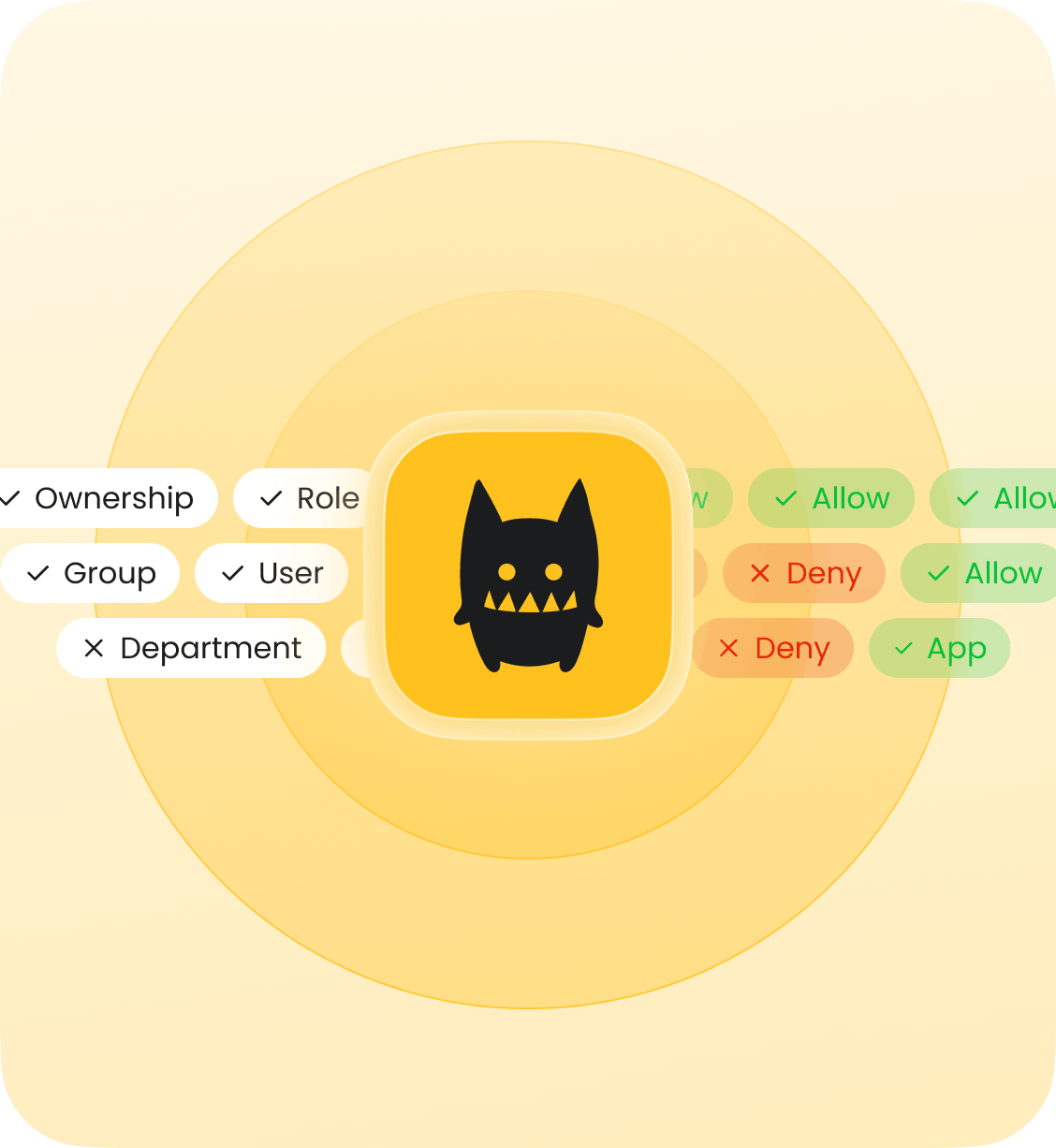
ABAC
RBAC
ReBAC
PBAC
Runtime
Event-time
Admin-time
Audit-time
Legacy systems
Cloud
Self-hosted
On-premise
Air-gapped
AI agents carry minimal identity context. Cerbos fills the gap.
When an agent acts on behalf of a user, Cerbos enriches the request with the user’s full identity, session, and resource context for fine-grained authorization decisions.
Identify the human behind every agent request
Synapse can fetch the delegating user's profile from your IdP and pass both identities to the policy engine in one call.
Evaluate agent and human together
One policy call evaluates what the agent is allowed to do and whether the user behind it is authorized to trigger that action.
No standing privilege for non-human identities
Access is never assumed from a previous decision. Every agent request is checked against the current policy at request time.
Let agents discover what's allowed
Query planning returns the full set of resources an agent can access on behalf of a user, with the same enrichment applied.
Full audit trail for every agent decision
Capture the enriched authorization request and decision outcome for full traceability across agent and human access decisions.
Developer-ready integrations
Works with your existing tools, workflows, and infrastructure
Identity provider enrichment
Fetch user profiles, groups, and attributes from Okta, Entra ID, Cognito, LDAP, and other identity providers.
Infrastructure integrations
Authorize access from API Gateways, messaging queues, data platforms, deployment pipelines, and other systems using the authorization protocols they support.
Data sources and databases
Retrieve identity and resource attributes from SQL databases, graph stores, and internal APIs.

Custom extensions
Build custom data sources, protocol adapters, and request transformations in any language that compiles to WebAssembly.
Dive deeper into authorization resources
Article
Introducing Cerbos Synapse
Guide
Securing AI coding agents

Guide
Authorization for legacy applications

Guide
Agent skill for writing authorization policies

Guide
Row-level security for Apache Trino
Cerbos Synapse
Authorization decisions are only as good as the data behind them
Enrich every request with identity, resource, and relationship context from your existing systems. No middleware to build, no custom adapters to maintain. Adopt incrementally with zero application code changes.