Permissions-aware authorization for RAG pipelines
Control what data enters your AI prompts. Cerbos enforces user-level permissions at the retrieval layer, so your RAG systems only surface information each user is authorized to see.
The retrieval problem
RAG pipelines expose data your users shouldn't see
Over-retrieval from vector stores
Embedding-based retrieval ignores authorization. A similarity search returns the most relevant chunks regardless of whether the requesting user has permission to see them.
Context injection into prompts
Unauthorized data retrieved from the vector store is injected directly into the LLM prompt. The model treats it as ground truth and surfaces it in its response.
Post-hoc filtering is brittle
Filtering results after retrieval means sensitive data has already been fetched, loaded into memory, and potentially cached. The security boundary was already crossed.
No audit trail for data access
Without authorization checks at the retrieval layer, there is no record of which data was accessed, by whom, or under what policy. Compliance teams have no visibility.
Built for production RAG systems
Permission-aware data filtering with Cerbos
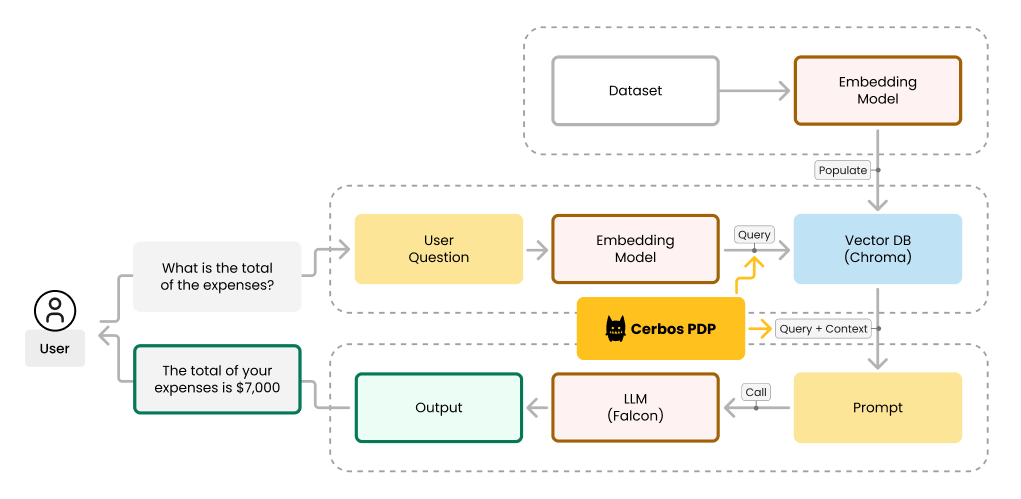
Cerbos integrates at the retrieval layer to ensure only authorized data reaches the LLM. The query plan API translates your authorization policies into database-native filters — applied before any data is fetched.
1
Define data access policies
Write YAML policies that define which principals can access which data based on role, department, region, classification level, or any attribute. Policies are version-controlled and testable.
2
Generate authorization-aware query plans
When a user triggers a RAG query, Cerbos evaluates their permissions and returns a query plan — a set of conditions that can be translated into native database or vector store filters.
3
Apply filters at the retrieval layer
The query plan is applied as a pre-filter on your vector store or database. Only data the user is permitted to access is retrieved.
4
Log every data access decision
Every authorization check is logged with the principal, resource, action, policy version, and outcome. Stream structured logs to your SIEM for compliance and forensic analysis.
How Cerbos secures your RAG pipeline
Filter before retrieval, not after. Cerbos translates authorization policies into native query filters so sensitive data never enters the pipeline.
Native vector store integration
Cerbos query plans translate into native filter syntax for Pinecone, Weaviate, Chroma, Qdrant, and FAISS. No custom middleware required.
Pre-retrieval enforcement
Authorization is enforced before data is fetched, not after. Sensitive data never enters the RAG pipeline or the LLM context window.
Sub-millisecond query plan generation
Query plans are generated in under a millisecond. Authorization adds negligible latency to the retrieval pipeline.
Same policies across all layers
The same YAML policies govern data access, API authorization, application permissions, and AI agent behavior. One policy engine, consistent enforcement.
Full audit trail for every data access decision
Trace every data access decision
Log which data was surfaced to which user through which RAG pipeline, with the exact policy version and conditions applied.
Policy lineage for every retrieval
See the exact policy, version, and release behind each data access decision for complete traceability.
Compliance-ready audit trails
Structured logs compatible with SOC 2, ISO 27001, HIPAA, PCI DSS, and GDPR audit requirements. Stream to your SIEM or log management platform.
Real-world scenarios
RAG authorization in practice
1
HR knowledge base
An employee asks the company chatbot about parental leave policy. Cerbos ensures the RAG pipeline retrieves only policies applicable to the employee’s region, employment type, and seniority level — not compensation data, termination procedures, or policies for other jurisdictions.
2
Multi-tenant SaaS documentation
A customer queries the support AI. Cerbos filters retrieval to only surface documentation, configuration guides, and known issues for that customer’s specific plan tier and product modules — not internal engineering docs or other tenants’ data.
3
Financial services research
An analyst asks an AI assistant about market positions. Cerbos enforces information barriers: the retrieval layer only returns research and positions the analyst’s desk is authorized to access, maintaining regulatory compliance with Chinese wall requirements.
Plug in and launch
Integrate with your AI and data stack
Vector stores
Enforce policy-based access for embeddings and retrievals across FAISS, Pinecone, Weaviate, Chroma, and Qdrant.
AI infrastructure
Deploy Cerbos policies alongside your AI model APIs. Works with OpenAI, Anthropic, Groq, and other inference providers.
SDKs
Use Cerbos SDKs to integrate authorization into your RAG pipeline with a few lines of code.


How teams use Cerbos to secure data access



“We rely on Cerbos to make authorization decisions across the whole mesh - millions of times a day. And it’s fast. We don’t even think about it anymore. It just works.”

Rob Crowe
Principal Engineer @Utility Warehouse
Months of dev time reclaimed by replacing scattered access logic with Cerbos PDP.
Eliminated technical debt from authorization.
Why enterprises choose Cerbos
Pre-retrieval filtering
Authorization is enforced before data is fetched, not after. Sensitive data never enters the RAG pipeline.
Authorization is enforced before data is fetched, not after. Sensitive data never enters the RAG pipeline.
Sub-millisecond decisions
Query plan generation adds negligible latency to the retrieval pipeline. Authorization at machine speed.
Query plan generation adds negligible latency to the retrieval pipeline. Authorization at machine speed.
Policy as code
YAML policies version-controlled in Git. Security teams can read and audit data access rules without specialized training.
YAML policies version-controlled in Git. Security teams can read and audit data access rules without specialized training.
Audit-ready logs
Every data access decision logged with full context. Meet SOC 2, HIPAA, ISO 27001 requirements out of the box.
Every data access decision logged with full context. Meet SOC 2, HIPAA, ISO 27001 requirements out of the box.
Learn more about RAG authorization
Article
Implementing authorization in RAG-based AI systems with Cerbos

Webinar
Securing agentic AI in production
Ebook
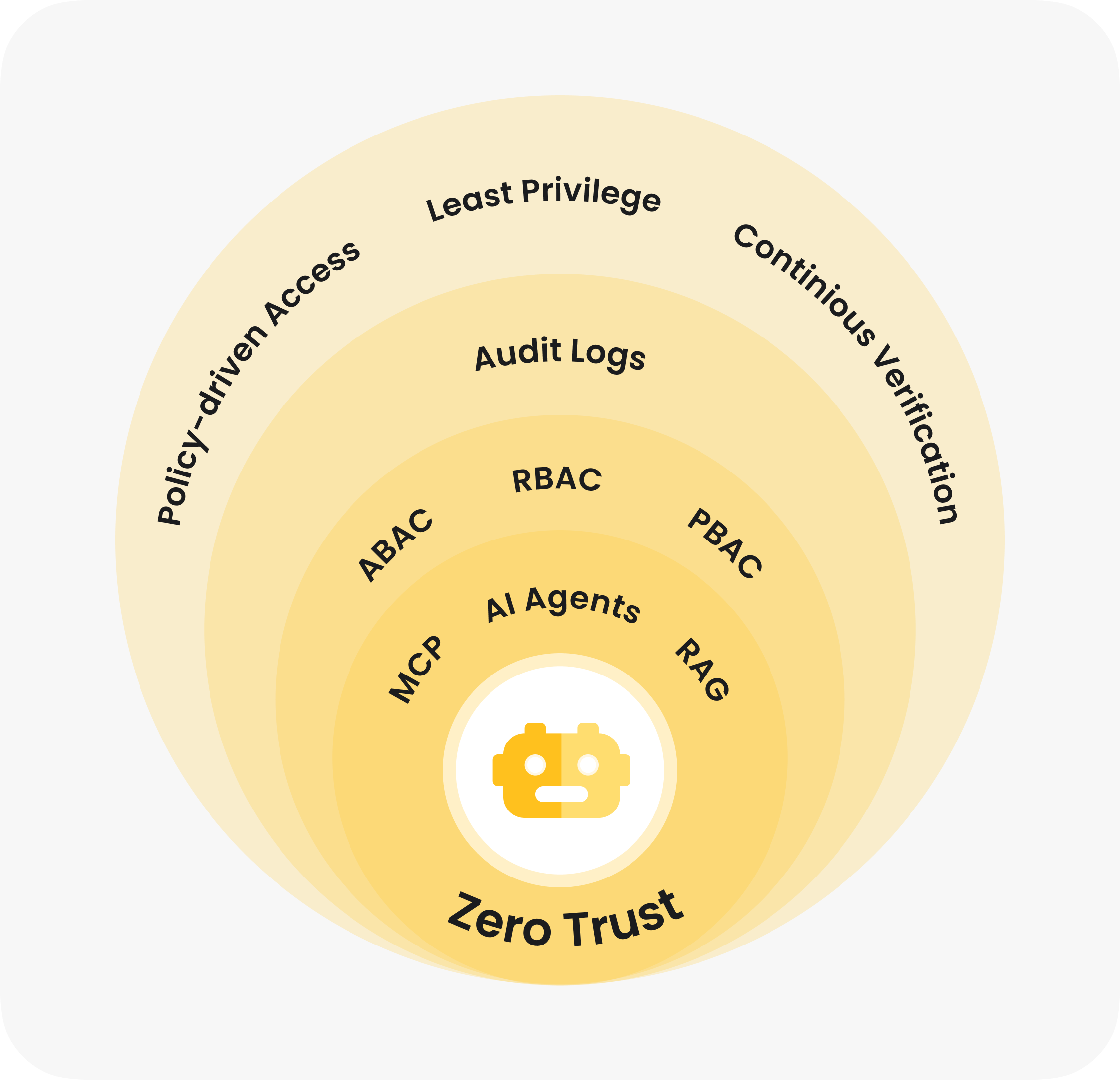
Zero Trust for AI: Securing MCP Servers

Ebook
Securing AI agents and non-human identities in enterprises

Article
MCP security & AI agent authorization
Article
MCP permissions. Securing AI agent access to tools
Ready to secure your RAG pipelines?
Our engineers will show you how Cerbos enforces user-level permissions at the retrieval layer.