From open-source policy engine to enterprise authorization management platform
Cerbos turns five this year.
Today, thousands of companies rely on Cerbos to manage complex permissions, enforce policies consistently, and control what AI agents are allowed to access and do. Every month, Cerbos processes more than 1.2 billion authorization checks every month. For many customers, it replaced millions of dollars a year in authorization development and management costs while giving security and compliance teams the audit visibility they need to stay compliant.
When we launched in 2021, the problem was simple to describe and hard to solve: engineering teams were embedding access control logic directly into application code. Access rules were scattered across services, tightly coupled to application logic, and impossible to change without a deployment.
We built an open-source Policy Decision Point to fix that. Thousands of teams started using it. Then they asked for more: a way to manage, test, version, and distribute access policies at scale, with full audit visibility into decisions and policy changes. We built Cerbos Hub.
Then came the harder problem: getting the right identity, resource, and relationship data to the policy engine reliably, without every team building their own pipeline to do it.
Now, with the introduction of our new data enrichment and orchestration layer, Cerbos Synapse, that problem is solved. Cerbos became an end-to-end authorization management platform, covering every part of access control from context enrichment to decision audit, across apps, infrastructure, and AI systems.
For security, IAM, and engineering leaders, that means authorization that keeps pace with how systems actually grow: new services, new infrastructure, new AI agents, all governed with a unified policy engine, data layer, and control plane.
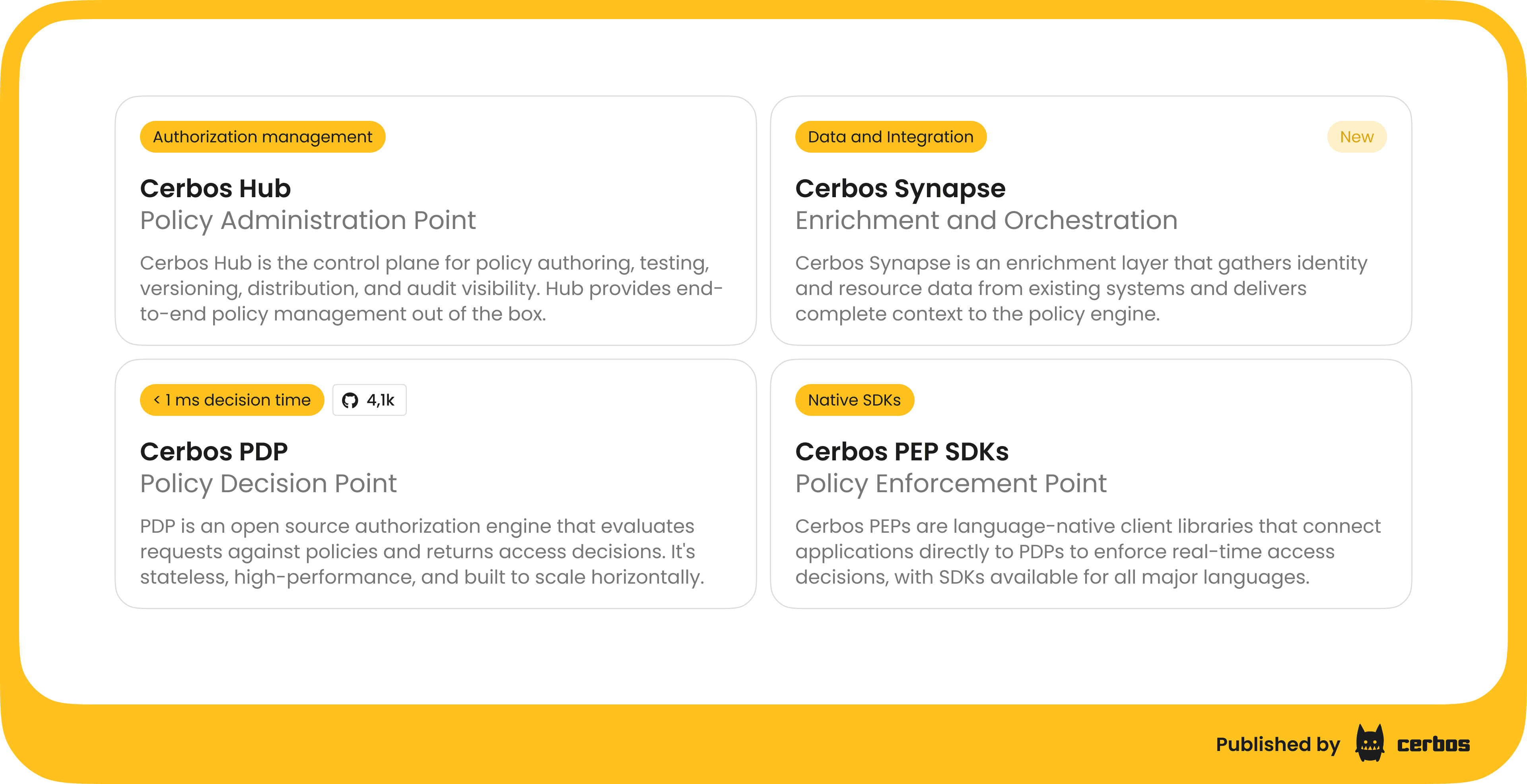
The Cerbos authorization management platform
Over the years, working with thousands of teams, we developed a clear view of what a complete authorization infrastructure looks like.
Authorization has four distinct problems: getting the right data to the engine, evaluating policy against it, enforcing decisions in applications, and managing policies at scale. Cerbos now has a dedicated component for each.
-
Cerbos PDP is the open-source authorization engine at the core of the platform. It evaluates authorization requests against policies and returns access decisions. It is stateless, lightweight, high performance, and AuthZEN compliant. It runs anywhere: containers, Kubernetes clusters, serverless, and at the edge.
-
Cerbos Hub is the control plane for policy authoring, testing, versioning, distribution, and audit visibility. It handles policy distribution across every PDP instance so updates propagate without restarts or redeployments. Security and compliance teams get full visibility into every authorization decision with structured audit logs that meet SOC 2, ISO 27001, HIPAA, PCI DSS, and GDPR requirements.
-
Cerbos PEP SDKs are client libraries that connect your applications directly to the PDP and enforce real-time access decisions. SDKs are available for JavaScript, Go, Python, Java, .NET, Rust, PHP, and Ruby.
-
Cerbos Synapse is the new component that completes the platform. It gathers identity, resource, and relationship data from your existing systems - identity providers, databases, graph databases, internal APIs - and delivers complete context to the policy engine before every authorization decision. Applications send a user ID; Synapse returns a fully enriched request. It also speaks the protocols that infrastructure systems like Envoy, Kafka, Trino, and Kubernetes already use, so those systems connect to Cerbos natively without custom adapters.
Together, these four components give enterprise teams a single governed layer for every authorization decision. What makes us proud is that teams who started with the open-source PDP naturally expanded to Cerbos Hub as their authorization needs grew, and now to Cerbos Synapse when the data problem hit. Our CPO and co-founder Alex Olivier describes it best:
Access control for every use case
Authorization shows up in different parts of the stack: application APIs, infrastructure, and increasingly AI-driven systems. Each introduces its own constraints, identity models, and enforcement points.
Cerbos platform covers all of these use cases out of the box, from a single platform with one source of truth.
| Use case | What it does | What it means in practice |
|---|---|---|
| Application permissions | Fine-grained, contextual access control for APIs and application logic | Define who can do what using roles, attributes, and relationships without embedding authorization logic in application code |
| SaaS multi-tenancy | Per-tenant authorization with isolated policy storage | Each tenant defines roles and permissions within platform guardrails, with updates propagated in real time across all PDPs |
| Non-human identity authorization | Policy-based access control for workloads and service identities | Enforce least privilege across microservices, APIs, and service accounts with full auditability of every decision |
| Dynamic policy management | Programmatic policy lifecycle management via APIs and SDKs | Create, update, validate, and deploy policies through CI/CD pipelines or system events without manual intervention |
| Product packaging | Policy-driven feature access and entitlements | Control feature availability, trials, and customer tiers without changing application code |
| Agentic AI authorization | Policy evaluation for AI agent actions | Evaluate both the agent identity and the delegated human context in a single decision before actions are executed |
| MCP server authorization | Externalized authorization for MCP tool access | Control tool usage per agent, per session, and per request without embedding logic inside the MCP server implementations |
| RAG pipeline authorization | Permission enforcement at the data retrieval layer | Ensure only authorized data is retrieved and passed into the LLM context window |
| Infrastructure authorization | Policy enforcement at the network and data platform layer | Authorize requests in API gateways, messaging queues, data platforms, and infrastructure using their native protocols, with no custom adapter code. |
Authorization in the age of AI agents
Five years ago, authorization was largely a human problem. Human users, human roles, human sessions. The policy engine needed to be fast and accurate, and the data was usually close at hand.
AI agents change both of those assumptions. An agent calling a tool on behalf of a user often carries minimal identity context: an agent ID, maybe a delegating user's subject claim, sometimes nothing beyond an API key. Without enrichment, the authorization request the policy engine receives is incomplete. The result is either over-permissive decisions or teams hard-coding context into agent configurations, which defeats the point of a centralized authorization platform.
The enforcement surface expands too. A single agent task can trigger dozens of authorization checks across different protocols and systems. It is not one API endpoint. It is every tool the agent can call, every resource it can access, every service it can invoke.
A single misconfigured permission does not affect one user. It affects every action that agent takes, across every system it can reach. This is why the same governance model that engineering and security teams rely on for human identities now covers AI systems too.
Available now
Cerbos Synapse is available today for Cerbos Hub customers. Organizations already running Cerbos can adopt it incrementally with no application code changes required.
Working integrations exist for Okta, AWS Cognito, Microsoft Entra ID, LDAP/Active Directory, Keycloak, Envoy, Istio, Kafka, Trino, and Kubernetes, with 13 reference implementations ready to use.
That is what the complete Cerbos authorization management platform delivers: authorization that works at every layer, for every identity, without the engineering overhead of building it yourself.
Book a free Policy Workshop to discuss your requirements and get your first policy written by the Cerbos team
Recommended content

Mapping business requirements to authorization policy
eBook: Zero Trust for AI, securing MCP servers

Experiment, learn, and prototype with Cerbos Playground
eBook: How to adopt externalized authorization

Framework for evaluating authorization providers and solutions

Staying compliant – What you need to know
Subscribe to our newsletter
Join thousands of developers | Features and updates | 1x per month | No spam, just goodies.
