Every enterprise has them. The payroll system from 2008. The vendor portal nobody wants to touch. The internal tool someone built in PHP a decade ago that somehow became business-critical. They hold your most sensitive data, and they have authorization controls that range from basic role checks to nothing at all.
You already know this is a problem. Your team probably flagged it in the last risk assessment. Maybe it came up during an audit. But when you raise it with engineering, the answer is always some version of the same thing: we can't modify that application.
And they're right. You can't add an SDK to a system you don't control. You can't refactor authorization logic that's been baked into application code for 15 years. You can't justify a full rewrite for a system that technically works. So the legacy apps stay ungoverned, the audit trail has gaps, and the risk sits there, quietly compounding.
The frustration isn't theoretical. Spend any time in security or identity forums and you'll see the same pattern. Engineers saying they have hundreds of applications in their environment, each with different authorization logic, different support groups, inconsistent SSO. Security teams describing "identity dark matter" in legacy systems, with local accounts and undocumented access paths that central governance can't reach.
SANS named authorization sprawl one of the top five most dangerous emerging attack techniques at RSAC 2025. The Verizon 2025 DBIR found credential abuse accounted for 22% of all confirmed breaches.
The gap between "we know this is a risk" and "we can actually do something about it" is where careers get exposed.
The problem isn't technical knowledge. It's practical options.
Most security and identity leaders have a clear picture of what good authorization looks like. Externalized authorization. Centralized policy. Runtime decisions based on identity, context, and risk signals. A single audit trail that covers every system.
The challenge has never been understanding the model. It's that the model seems to require something impossible: modifying the applications.
This is the argument that kills most authorization modernization initiatives before they start. Engineering teams look at the legacy estate and see a rewrite. Security teams see a governance gap they can't close. Identity teams see fragmented authorization logic scattered across codebases they don't control. Everyone agrees it should be fixed. Nobody agrees it can be.
So nothing happens. The legacy systems keep running with whatever access controls were built in originally. The JML lifecycle covers role assignment in your IdP but doesn't reach the fine-grained permissions hardcoded into those applications. Terminated employees might keep access until someone manually remembers to disable their local account. And the next audit requires the same scramble to produce evidence that doesn't really exist.
What changes when you don't need to modify the application
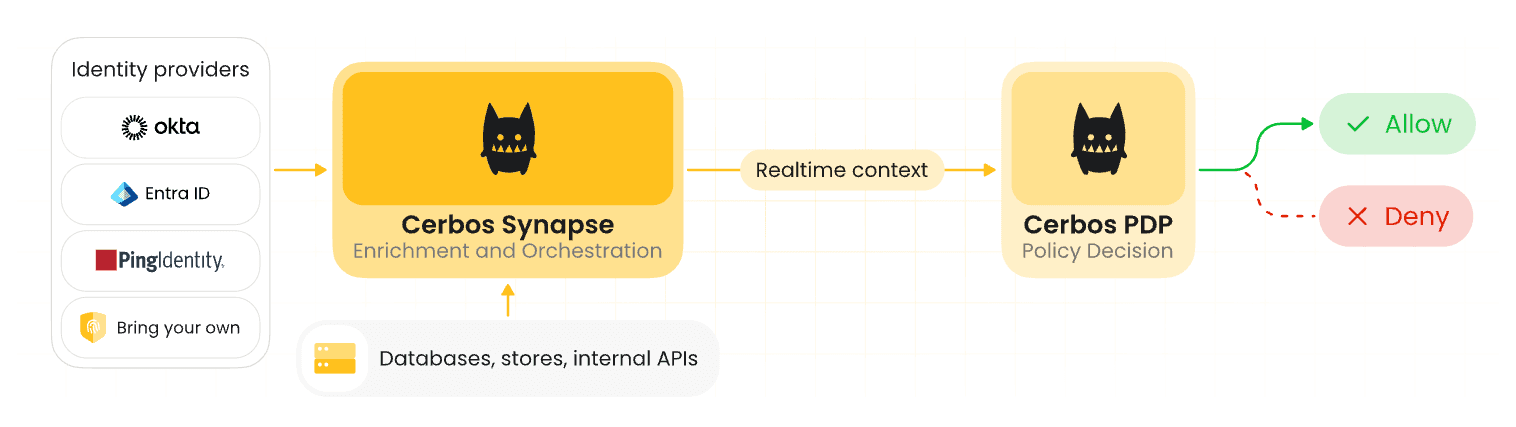
Cerbos Synapse takes a different approach. Instead of requiring code changes inside the legacy application, it places an authorization layer in front of it at the network gateway.
The application doesn't change. It doesn't need to know about Cerbos. It doesn't need an SDK. A reverse proxy (such as Envoy) sits in front of the application, handles modern authentication against your identity provider, and calls Synapse for an authorization decision on every request. If the policy allows it, the request reaches the application. If it doesn't, the request is blocked before the application even sees it.
This means your team can start governing legacy applications this week, not after a multi-quarter rewrite. The same policy language, the same Hub instance, the same audit trail you use for your modern services now covers the legacy systems too.
For identity teams, this is significant. Your IdP becomes the source of truth for who can access what, even in systems that were never designed to integrate with it. Change someone's role in Entra ID or Okta, and their access to the legacy payroll system changes on the next request. No local account management. No manual deprovisioning. The JML lifecycle finally reaches the applications it was always supposed to cover.
Visibility you've never had
Before any of this, you get something that might matter even more: visibility.
Deploy Synapse in observe mode - where every decision is allowed - and every request to the legacy application becomes an audited authorization event. Who accessed which routes, when, with what roles, from what device, allowed or denied. All of it flowing into Cerbos Hub alongside the audit data from your modern services.
For most organizations, this is the first time anyone has had a clear picture of how these legacy systems are actually used. It's the same pattern Utility Warehouse saw across their 4,500-service mesh. Before you write a single deny rule, you can answer questions that were previously unanswerable. Which accounts are accessing the admin routes? Is anyone hitting sensitive endpoints from unmanaged devices? Are there access patterns that don't match any known business process?
For compliance, this closes gaps that auditors will otherwise flag. The systems that are hardest to govern are usually the ones holding the most sensitive data: payroll, HR records, financial reporting. Getting structured audit coverage over these systems, even at the route level, is the difference between a clean audit finding and an open remediation item.
Utility Warehouse, a FTSE 250 company with 4,500 services, went from zero authorization visibility to full observability across their entire mesh in a single deployment. By placing Cerbos as an authorization proxy in front of all their services at once, they got a unified audit trail covering every decision, millions of times a day. Read the full success story.
Context-aware decisions, not just role checks
Basic role-based access is a start, but it's not where this stops. Synapse can pull in additional context at decision time through data source extensions. Device posture from your MDM. Risk scores from your IdP. Employment status from your HR system. Geolocation. Time-of-day restrictions.
This means you can write policies like "only allow access to the payroll system from managed devices with disk encryption enabled" or "block access for any session flagged as high-risk by the IdP" or "restrict admin routes to business hours only." All of this happens at the gateway. The legacy application never needs to know about any of it.
For security teams working toward Zero Trust, this is how you extend continuous, context-aware enforcement to the systems that were previously outside your governance reach entirely. Authentication was already solved. Fine-grained, runtime authorization was the gap. This closes it for legacy systems without waiting for engineering to find time for a rewrite.
The conversation changes
The reason legacy authorization stays broken isn't that nobody knows it's a problem. It's that the available solutions all required something that couldn't happen: modifying the application.
That constraint is real. But Synapse removes it from the equation. And once it's removed, the conversation between security, identity, and engineering teams shifts. It stops being "we need to rewrite these applications" and starts being "we need to deploy a proxy and write some policies." That's a fundamentally different project. Different timeline, different risk profile, different likelihood of actually happening.
The systems you can't rewrite are the ones that need governance the most. They hold your most sensitive data. They have your weakest access controls. And until now, they've been the hardest to bring into any centralized authorization framework.
That's no longer the case.
Book a call to see how Cerbos can bring your legacy applications under the same authorization governance as the rest of your estate.
Go deeper:
- How to adopt externalized authorization (eBook) for a step-by-step playbook on moving authorization out of application code
- The IAM security checklist for 2026 (Checklist) for a practical framework covering authorization governance gaps
See it in action: Watch the technical walkthrough of Synapse wrapping a legacy payroll application with gateway-level authorization, or read the technical blog on how the gateway pattern works.
FAQ
Tagged in