In the previous article, I showed how embedded authorization logic leads to enforcement drift, audit gaps, and delayed incident response in digital banking products. Under increased transaction volume and AI-driven execution, those weaknesses scale.
The structural issue is that authorization logic remains embedded inside individual services. As long as enforcement is service-specific, consistency of access policy evaluation cannot be guaranteed at runtime.
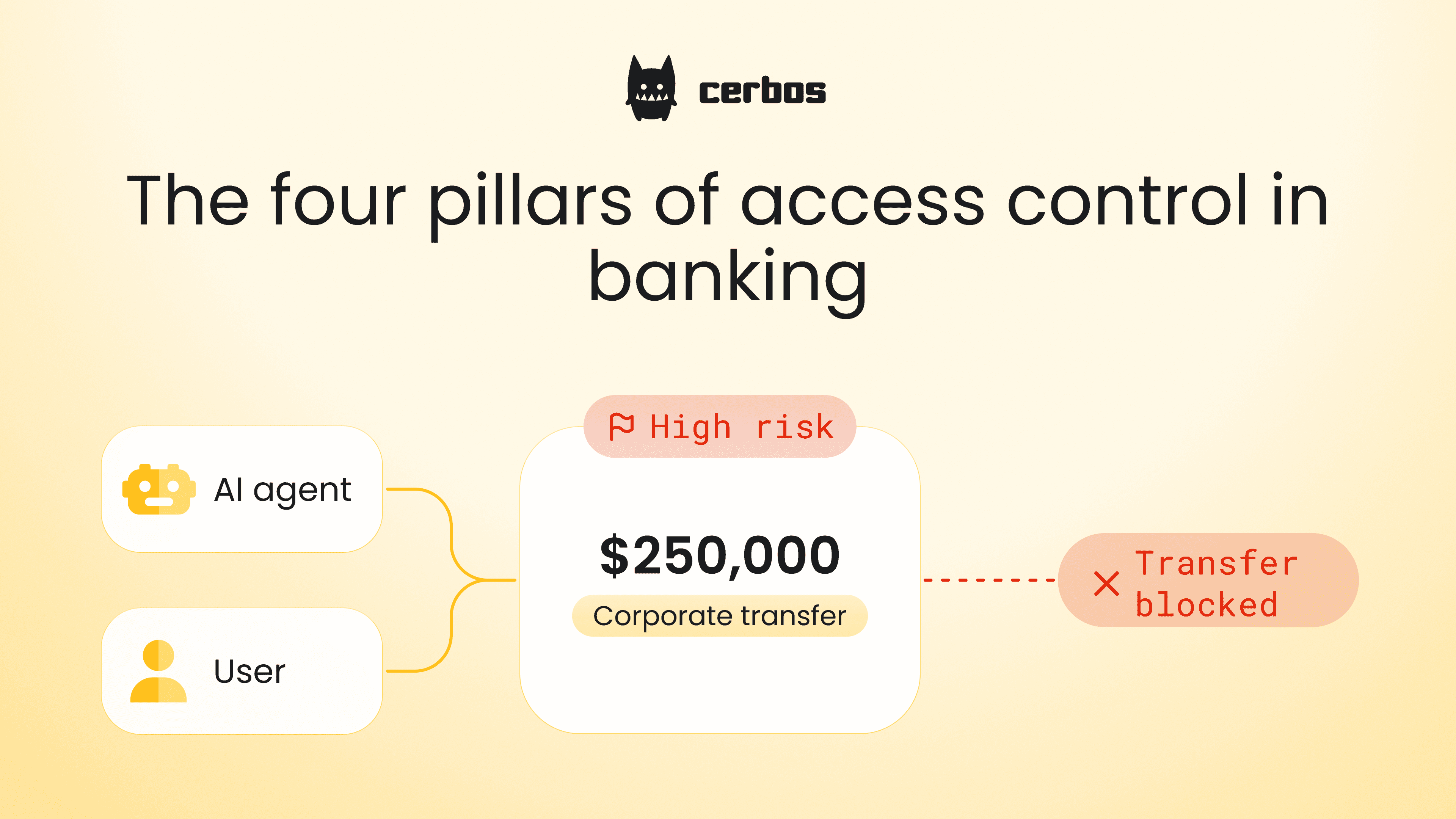
Externalized, policy-based authorization introduces a centralized control layer enforced at runtime across human users, services, and AI agents. In regulated banking platforms, this access control model must address 4 pillars:
- Policy development
- Policy deployment
- Zero Trust authorization
- Full auditability
Each pillar addresses a specific control failure outlined in my risk analysis article. Getting those four pillars right is a control requirement, not a design preference.
Let’s dive deeper into each of those:
Centralized policy development from day one
When a banking platform is built by dozens of engineers shipping microservices in parallel, access rules tend to diverge across services. Over time, those differences lead to inconsistent access decisions across systems. Centralized policy management addresses that risk at its source. With externalized authorization using Cerbos, you can:
- Separate authorization logic from application code so access rules are defined once and enforced consistently across services.
- Use RBAC, ABAC, and relationship-based models to define approval chains, transaction limits, regional constraints, and role hierarchies without custom logic in each service.
- Manage authorization policies through Git, ensuring every change is reviewed, tested, and validated before reaching production.
- Test policies independently of application releases.
The outcome for a bank building a new digital platform is a centralized permission management layer. New services inherit the same authorization rules by default, instead of introducing parallel implementations across payment, lending, and internal systems.
Policy deployment with full traceability
Access policy changes must move from development to UAT to production through a defined and traceable process. Each environment should run a clearly versioned policy bundle. When a policy is promoted, it must be clear what changed, when it changed, and which policy version is active in each environment.
Between 2023 and 2025, the UK Treasury Committee reported more than 800 hours of unplanned IT outages across major banks, with several incidents linked to internal system failures and change processes rather than external attacks. Under regulatory review, change management and configuration control were central themes. This is the environment in which access policy deployment must operate.
In one recent case, Barclays reported that during a multi-day outage, 56% of online payments failed due to severe degradation in mainframe processing performance. The bank estimated compensation costs between £5 million and £7.5 million.
Real incidents show that production changes and system configuration failures have a direct financial and regulatory impact. Acees policy deployment must operate within the same level of governance and traceability. To reduce exposure to these types of risks, we built Cerbos with capabilities that allow you to:
- Move authorization changes from dev to UAT to production with a complete, auditable history of what changed and when.
- Eliminate manual copy-paste between environments that leads to configuration drift.
- Distribute the same approved policy bundle to connected services, reducing environment and region-level drift.
- Revert to a previously approved authorization version without modifying application code.
Zero Trust authorization enforced at every decision point
Zero Trust means no access request is trusted by default, even inside the internal network. Every call must be evaluated against an explicit access policy based on identity, action, resource, and context. Zero Trust model is built on the following principles:
| Always verify | Every payment instruction, or customer data request is evaluated at runtime. |
|---|---|
| Continuous verification | Identity, device posture, session context must be reassessed throughout the interaction, not only at login (especially for high-value transfers and sensitive data access). |
| Policy-driven access | Access decisions are enforced through explicit policy rules rather than implicit trust or hardcoded service logic. Learn more about policy-driven access here. |
| Least privilege access | Employees, service accounts, and AI agents receive only the permissions required for a specific banking action. Standing broad privileges across payment or ledger systems are avoided. |
| Network segmentation | Core banking services, payment processors, customer data systems, and analytics workloads are segmented to limit lateral movement between environments. |
| Assume breach | The architecture is designed under the assumption that compromise is possible. Controls focus on containment, visibility, and runtime enforcement. |
Implementing these principles in a production banking environment means externalizing the enforcement layer. That's what Cerbos is designed to do:
- Reduce the risk of unauthorized fund movement and approval bypass by enforcing least privilege on every request.
- Maintain control as transaction volumes and digital channels expand, without introducing operational bottlenecks.
- Evaluate human users, service to service calls, background jobs, and AI agents under the same policy model.
- Eliminate a single point of failure in authorization and avoid future architectural redesign as transaction volume grows.
- Ensure every payment, limit change, and data access is explicitly authorized and traceable.
Clear auditability. Prove who had access to what, and when
Regulators and internal audit require verifiable evidence of access control. Each authorization decision must be traceable to a specific identity, action, resource, and policy version. When that linkage is missing, investigation relies on log correlation across multiple services.
Implementing auditability at the permission management layer means every decision produces a structured, policy-linked record at the point of enforcement. That's the problem Cerbos solves for banking compliance:
- Log every authorization decision with subject, action, resource, and outcome.
- Link each decision to the exact policy version in effect at that moment.
- Use decision records for both compliance reporting and incident investigation.
- Stream structured decision logs into monitoring and SIEM systems.
The outcome is immediate, policy linked evidence of access control decisions. Authorization can be demonstrated to every auditor with exact decision context, without manual reconstruction across services.

These four pillars are not independent design choices. Each one closes a specific control gap that embedded authorization cannot address. Together, they define what externalized, policy-based authorization must do in a regulated banking platform: at runtime, across every service, for every request.
FAQ
Tagged in