When your identity systems multiply and no one has the full picture, security and compliance suffer. Fragmented IAM gives organizations a false sense of control…until the audit fails or an incident reveals the gaps. In this blog, we break down why this happens and how continuous governance offers a better way forward.
This post is part of a series based on a conversation between Aram Andreasyan, Head of Solutions at Cerbos, and Giao Nguyen, IAM advisor at 1Kosmos. Giao brings decades of firsthand experience advising enterprises on complex identity rollouts, audits, and governance programs. Together, they explored why identity has become such a pressure point for CISOs, and what it actually takes to build maturity in this space.
What follows is a distilled, actionable summary of that discussion, focused here on a growing problem: IAM sprawl, visibility blind spots, and the operational chaos that hides in plain sight.
In our second post in this series we tackle a related silent threat: "privilege creep" - the buildup of excess access that can turn into a ticking time bomb. In our third post, we break down how to implement real-world, risk-aware access controls that move beyond check-the-box Zero Trust.
The identity tool sprawl problem
Modern enterprises often have a patchwork of identity and access management tools - HR directories, Active Directory/LDAP, single sign-on platforms, cloud IAM consoles, identity governance suites, etc. Over years, new apps and acquisitions add even more. This leads to operational complexity, poor visibility, and “identity silos”. This sprawl creates dangerous blind spots.
It’s easy for a CISO to assume all those tools mean IAM is under control. But more tools can mean no single source of truth. Data gets scattered across directories and databases that don’t talk to each other. One IAM executive admitted to running 45 different identity systems, then lamented: “I know who the users are, but I have zero visibility into what they actually do once they’re inside.” In other words, they could provision accounts but couldn’t easily track usage or monitor activities across siloed systems.
Such blind spots give a false sense of security. Leaders might feel their IAM program is mature - “we have all these solutions deployed” - yet basic questions go unanswered. Who approved a certain admin access? Which entitlements does John Doe actually use, and which are sitting idle? With fragmented data, answering these can be problematic, to say the least.
Blind spots come to light at audit time
One place these issues surface is during compliance audits. Disconnected logs and consoles turn audits into firefights. As Aram observed, when an audit lands, “the logs are so fragmented, no one can tie a decision to a particular policy anymore.” The team scrambles in last-minute mode, exporting spreadsheets from multiple systems and reconciling records by hand - often with a lot of finger-pointing in the process.
Does this sound familiar? It’s end of quarter, and auditors ask: “Prove only authorized users can access finance data. Show who approved each access.” If identities and approvals live in five or six different silos, the security team ends up manually stitching together evidence from HR apps, ticketing systems, AD logs, etc. Despite having “state-of-the-art” IAM products, the organization isn’t audit-ready: it’s in reactive mode.
Many companies that pass audits on paper still get breached because passing an annual audit doesn’t mean you have continuous control. Audits often only check that processes exist, not that they’re effective day-to-day. A company might boast that it conducts quarterly access reviews, but if those reviews are cursory rubber-stamp exercises, problems linger between checkpoints. As IAM advisor Giao Nguyen put it, some firms only leverage governance tools to meet the bare minimum (“check the box”) for compliance, without actively using them to manage risk daily.
The results that privileged access accumulates unchecked, and anomalies go unnoticed until a crisis. Meanwhile, leadership operates with a false confidence that “we have IAM covered because we have tools X, Y, Z and passed our last audit.” It’s precisely these gaps that attackers love to exploit.
Why IAM fragmentation undermines security
Identity fragmentation not only creates work for audits, but it also directly undermines security and compliance in several ways.
Incomplete visibility
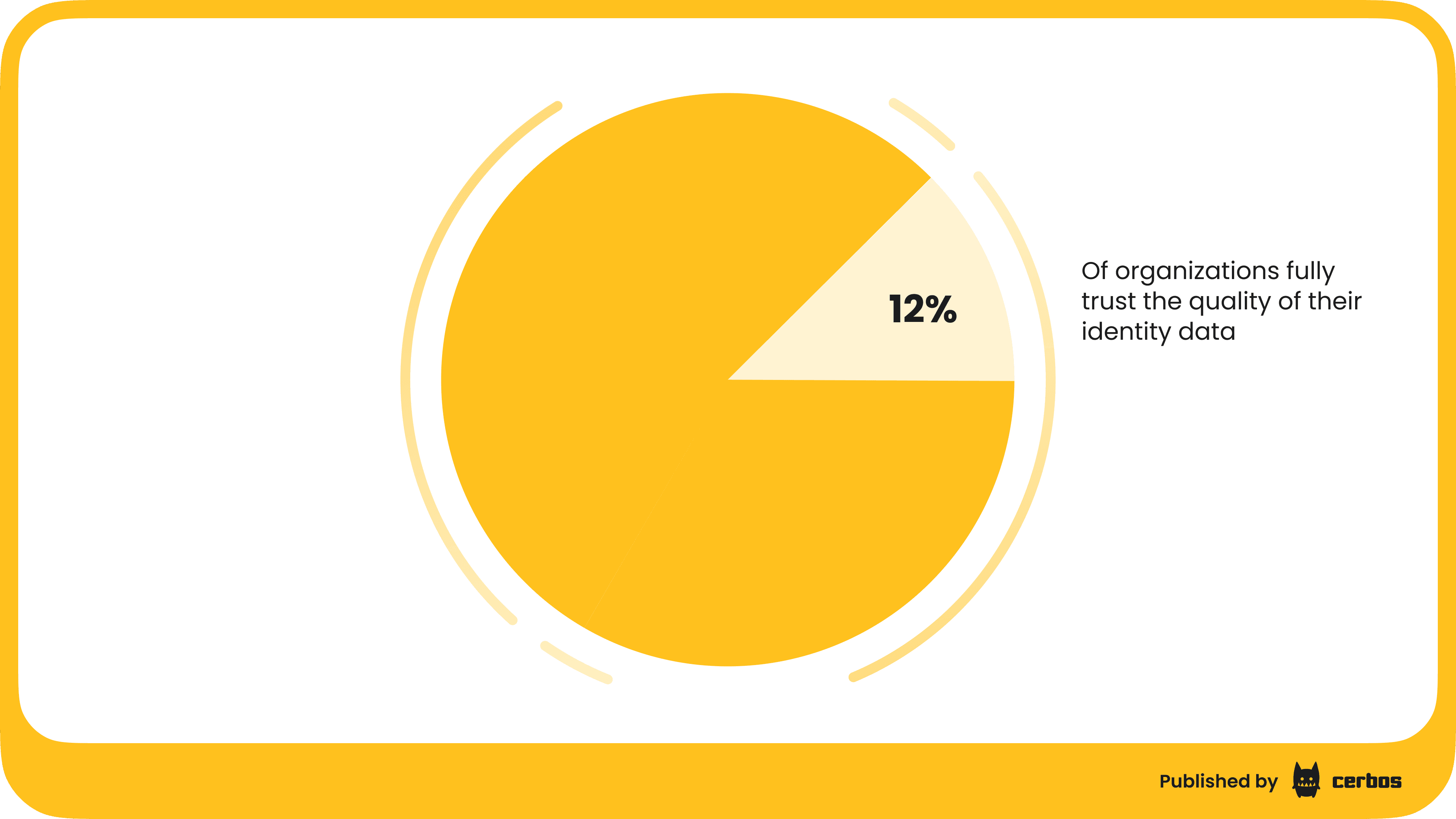
If each system holds a piece of the puzzle, no one has a 360° view of who has access to what. An employee’s account might be disabled in AD but still active in a SaaS app; a user might be removed from one database but lingering in another. These orphan accounts or inconsistent entitlements become ripe targets. The average enterprise knows this intuitively: in one poll only 12% of organizations fully trust the quality of their identity data, meaning nearly 9 in 10 suspect their IAM records are incomplete or outdated. It’s hard to govern what you can’t reliably enumerate. Bad data → bad decisions, as the saying goes.
Stale and inconsistent policies
With multiple IAM platforms, you often get multiple policy engines - one for SSO roles, another for your legacy apps, separate admin permission sets in each cloud, etc. It’s difficult to enforce a unified access policy. One system might allow something that another would flag, and there’s no single brain coordinating them. This inconsistency can lead to gaps where an attacker finds the weakest link.
Delayed response
If you can’t easily pull consolidated identity activity logs, detecting and responding to incidents is slower. Consider a scenario: a user’s account is compromised and used to access sensitive data. In a unified system, security could quickly see all the systems the account touched and cut off access. In a fragmented environment, by the time you’ve gathered logs from each tool, the attacker could have a field day. This is why identity-related breaches are so prevalent - they slip through the cracks. (84% of companies have suffered an identity-related breach in 2021, according to the Identity Defined Security Alliance.)
Audit and compliance risk
Regulations from SOX to GDPR increasingly require proof of strict access controls and traceability. If your team is rushing to assemble records during an audit, things can be missed. Worse, a failed audit or undiscovered access violation can have legal and financial consequences. For example, if an auditor finds that you cannot produce an approval trail for privileged accounts, it will raise red flags. Continuous governance is becoming an expectation from regulators that security controls be operating effectively all the time, not just at audit checkpoints.
Continuous governance: A “live” view of IAM
The antidote to these issues is adopting what Aram and Giao call continuous governance - moving from periodic, reactive identity management to a dynamic, ongoing assurance that the right controls are in place. The vision is that an audit shouldn’t be a fire drill at all, but almost a non-event. If you have continuous governance, producing evidence is as simple as clicking “export report”, not performing heroic data archaeology.
What does continuous IAM governance look like in practice? At its core, it means every access change, every entitlement, every policy decision is evaluated and logged in real time. Rather than relying on after-the-fact reviews or assumptions, the organization maintains a near real-time state of compliance. Here are key elements:
Centralized identity inventory
First, integrate and consolidate identity data. Ensure all those disjointed directories and cloud IAM portals feed into a single source of truth, or as close to one as possible. This could be a unified identity governance system or a data layer that aggregates identity info from various sources. The goal is to be able to query “show me everything user X has access to” or “who has role Y across all systems” in one place. Many organizations are investing in this integration: building an identity data fabric, reconciling duplicates, and mapping orphan accounts. It’s not glamorous work, but cleaning up identity data pays dividends when you can finally trust your reports.
Real-time logging & traceability
Every time someone’s access changes, it should leave an auditable trail immediately. For instance, if a user is added to an admin role or a permission is elevated, the system logs who approved it, when, and why. Nothing should “slip through” via an out-of-band process. If a ticket or request was the basis for the change, that ticket ID is tied to the change record. This way, when an auditor, or your own team, asks “Why does Jane have access to System X?”, you can answer in minutes with concrete evidence: Jane was granted access on March 3 by approval of her manager via ticket #12345. No more digging through email approvals or Slack messages. It’s all captured.
Policy-as-code & unified enforcement
Adopting policy-as-code can be transformative. This means codifying your access rules and business logic in a way that’s enforced uniformly across environments. Instead of having one rule in AD, another in AWS IAM, and yet another informal rule in a spreadsheet, you define policies in a central engine and have apps consult it for decisions. For example, you might encode: “If a user is inactive for 90 days, automatically revoke their access” or “Only managers can approve role changes for finance data.” Platforms like Cerbos allow you to write such rules as code and hook them into your applications and services where the decision will be enforced. The benefit is twofold: 1) Consistency - the same policy is applied everywhere, reducing variance between tools; and 2) Auditability - you can point to a policy file and the system logs to show that “User X’s access was removed after 90 days of inactivity per policy ABC,” with the system enforcing it. Unified authorization layers ensure no decision is made in a vacuum: it’s always tied back to a governing policy.
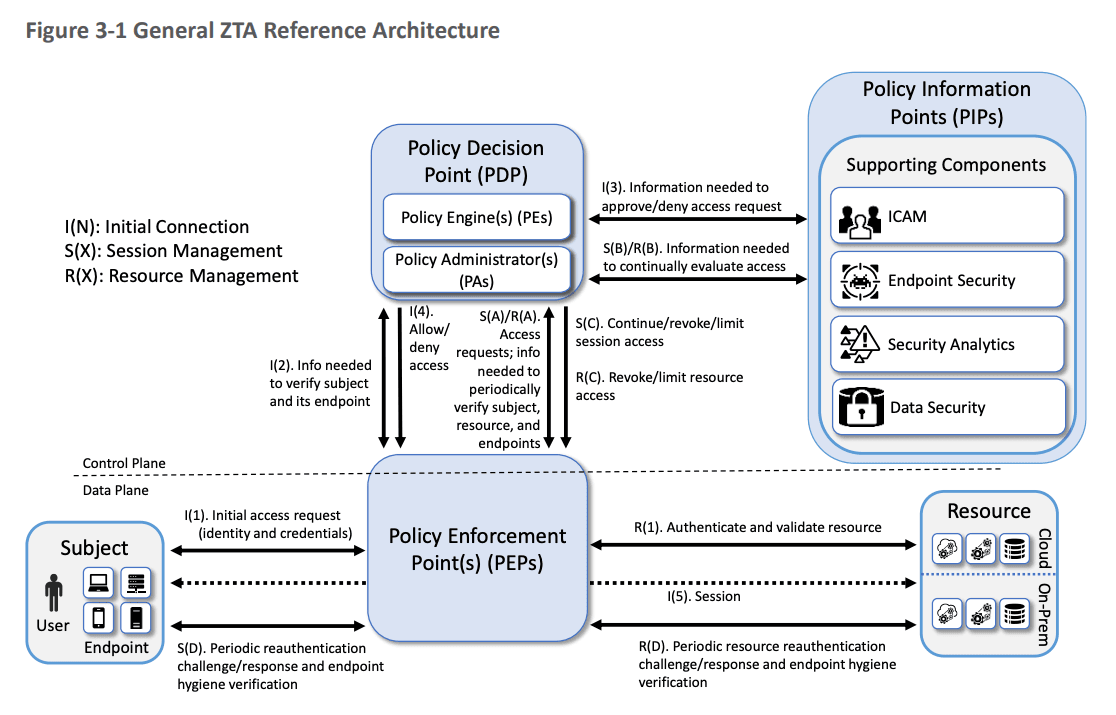
Source: NIST Special Publication 1800-35, Implementing a Zero Trust Architecture
Continuous monitoring and alerts
Rather than annual or quarterly reviews that gather dust, continuous governance involves ongoing monitoring for anomalies or policy violations. For instance, implementing a Cloud Infrastructure Entitlements Management tool to continuously scan cloud permissions for unused or excessive rights. Or setting up automated jobs that flag any account dormant for over 90 days, any new admin account created outside of the standard process, etc. When a risky condition is detected, an alert or automated action should trigger immediately, not weeks or months later. Some organizations now do rolling access reviews - a subset of permissions reviewed every month - to avoid the year-end pileup and catch issues early. The idea is to smooth out the peaks and make oversight part of business-as-usual.
Fast, automated remediation
In a mature continuous governance setup, the response to findings is also automated where possible. If an account is identified as orphaned (e.g. belonging to a departed employee), the system could automatically disable it and notify the IAM team. If a policy violation occurs, say someone manually added a user to a high-privilege group outside the proper workflow, an automated process might remove that addition and open an incident for investigation. The more you can trust the system to take immediate corrective action, the less you’re reliant on an overworked admin noticing something in a report. One forward-leaning approach is just-in-time access provisioning with automatic expiry. Instead of giving permanent access and later trying to remember to remove it, you grant access for a defined duration or until a project’s end, and the system revokes it when time’s up. This “expire by default” model preempts the accumulation of excess privileges (a concept we’ll revisit in the next blog on privilege creep).
Crucially, continuous governance is not one-size-fits-all; it scales to your risk profile. A high-regulated bank might pursue near-real-time monitoring of every access change, whereas a tech startup might start with monthly snapshots. The key is the mindset shift: from seeing governance as a periodic checkbox exercise to making it an ongoing, embedded practice. As Giao noted, CISOs are increasingly pushing for an “always audit-ready” stance, rather than scrambling once a year. Even if your organization isn’t there yet, you can begin moving the needle. For example, by increasing the frequency of access reviews, integrating one additional system’s logs into your central SIEM, or automating one manual approval process at a time.
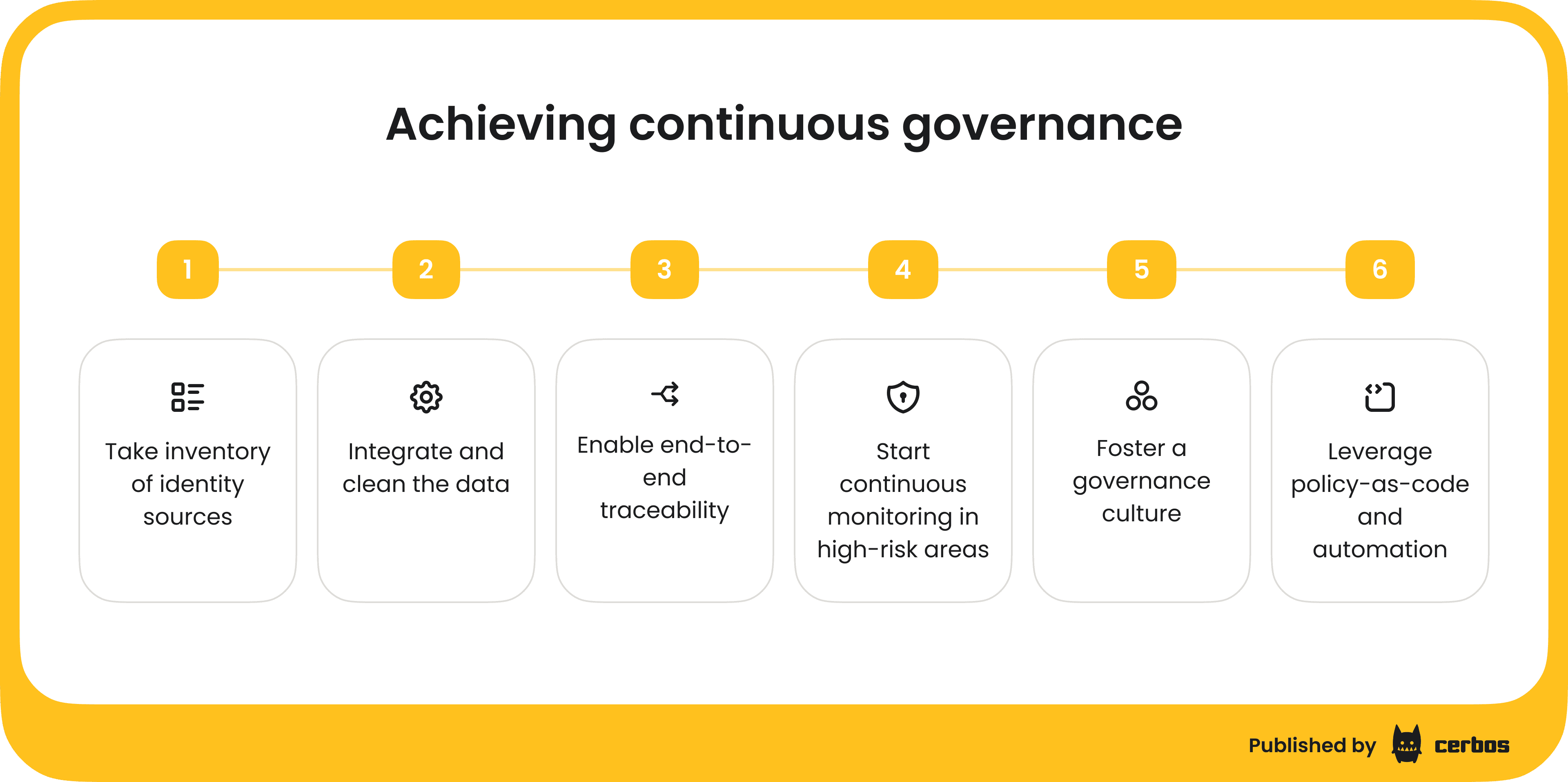
Making it happen: Steps for CISOs
How can a CISO break the cycle of fragmentation and achieve continuous governance? A few actionable steps:
1. Take inventory of identity sources
Catalog all the places where identity and access data reside. You may be surprised (Shadow IT databases, legacy apps). This inventory sets the stage for integration. Identify any “blind” sources that aren’t monitored.
2. Integrate and clean the data
Work towards an aggregated identity store or reporting dashboard. This could mean deploying an identity governance platform if you don’t have one, or using your security analytics tools to pull in feeds from various identity systems.
Simultaneously, initiate a data hygiene project - fix or eliminate duplicate accounts, update incomplete records, and remove obsolete accounts. It’s estimated that a huge portion of identities in any given organization are stale or unused - for example, over 90% of identities use less than 5% of the permissions they have (more on that statistic in our next post of the series). Cleaning up that clutter will make your governance reports far more accurate.
3. Enable end-to-end traceability
Ensure that for any access change, you can answer who, what, when, and why. If your current tools don’t enforce tying approvals to changes, consider process tweaks or tools that do. Even a simple internal mandate, e.g. all admin access requests must go through the ticketing system, can create an audit trail. Then integrate those tickets with identity changes. The goal is that any curious or compliance-minded person can trace a straight line from a user’s permission back to a documented approval (or policy) in one system of record.
4. Start continuous monitoring in high-risk areas
You don’t have to boil the ocean. Identify your crown jewels or highest risk identity domains (perhaps cloud infrastructure, production databases, or privileged IT accounts). Implement a continuous oversight mechanism there first. For example, deploy a CIEM tool to monitor cloud IAM roles, or turn on a feature in your IGA product to automatically flag toxic combinations of access. Demonstrating quick wins in a critical area will build support for expanding the approach.
5. Foster a governance culture
Technology alone won’t solve it. It’s also about people and process. Break down silos by forging partnerships between security, IT, HR, and application owners. Governance is a team sport; the IAM team needs timely information, like who’s leaving the company, or when a new app goes live, and cooperation from others. Educate stakeholders that these efforts aren’t about bureaucracy but about preventing incidents that could harm everyone. Giao Nguyen emphasizes that when other departments see security as a helper rather than a roadblock, they’re far more willing to feed you the data and support needed for continuous governance. Sometimes simply sharing audit pain points - “hey, last audit we spent 100 hours chasing down evidence, which affected everyone’s projects” - can motivate teams to streamline things proactively.
6. Leverage policy-as-code and automation
Look at where manual processes are bogging down your identity management: e.g. managers forgetting to remove contractors, or IT having to manually disable accounts. These are opportunities for automation and policy enforcement. For instance, if “contractor access expires after 90 days” is a policy, implement that in code so it happens automatically. Consider dynamic authorization solutions like Cerbos to externalize these rules from individual apps and enforce them centrally. That not only reduces human error but also gives you a clear, codified set of access rules to show auditors or regulators. As a bonus, policy-as-code systems often come with audit logs and decision records, which can dramatically simplify compliance reporting - you can show not just what decision was made, but why. E.g. “Access denied because device posture was untrusted, per policy XYZ”.
Finally, measure progress. Set metrics for your IAM program’s visibility and responsiveness - for example, track how many orphan accounts you eliminate each quarter, or how long it takes to deprovision access when someone leaves. If those numbers improve over time, you’re gaining maturity. The aim is that security leadership can confidently answer questions at any moment about who has access to what and why. When a board member or regulator comes calling, you don’t want to respond with “Give us a week to pull the data” - you want to click a button and produce a credible, up-to-date report.
Turning on the lights
Overcoming IAM blind spots requires effort, but the reward is peace of mind. When you consolidate your identity data and adopt continuous governance, you flip on the lights in a room that was dimly lit. You can see who has access across the organization, correct course quickly, and credibly demonstrate control to auditors, executives, and yourself as CISO. Instead of hoping nothing falls through the cracks, you know that issues will be caught and addressed in real time.
Regulators and attackers alike are laser-focused on identity, so this level of visibility and agility is fast becoming non-negotiable. As Gartner forecasted, 75% of security failures now stem from inadequate identity, access, and privilege management - meaning if we get IAM wrong, everything else can crumble. Continuous governance is about getting IAM right, continuously. It turns identity from a lurking liability into a strength: a program that not only checks the compliance boxes but actively reduces risk every minute of every day.
CISO takeaway: Don’t let tool sprawl and data silos keep you in the dark. Start building a single pane of glass for identities and a culture of constant oversight. When governance is continuous, surprises are few - and audits, or breaches, won’t catch you off guard.
Check out the next post in this series, where we tackle a related silent threat: “privilege creep” - the buildup of excess access that can turn into a ticking time bomb.
Tagged in