Get visibility and control over what every user, service, and AI agent can do
Authorization for identity leaders who need to modernize access control, and secure AI before it ships.
The authorization layer your IAM stack is missing
Your IdP authenticates. Your IGA provisions roles. Cerbos controls what identities actually do at runtime.
Govern every identity type
Unified policies for users, service accounts, NHIs, and AI agents. One place to manage access across your entire identity fabric.
Your board has mandated AI. Your job is to make it safe
Define what each AI agent can access before it goes live - and revoke that access in seconds through policy if anything changes.
“We rely on Cerbos to make authorization decisions across the whole mesh - millions of times a day. And it's fast. We don't even think about it anymore. It just works.”

Rob Crowe, Principal Engineer
How authorization becomes your identity blind spot
You know who your users are. But what can they actually do? The authorization decisions inside your applications are fragmented, hardcoded, and invisible - creating gaps that auditors find and attackers exploit.
Your IdP stops at authentication
It verifies who someone is. But what they can do - at the resource level, at runtime - is scattered across application code, invisible to governance.
JML processes don’t reach permissions
Your IGA provisions roles. But the actual authorization decisions - what data users see, which actions they perform - live in code, outside your identity lifecycle.
The board bought AI. You inherited the access risk
Agents inherit broad permissions, mask who initiated actions, and create access paths your existing IAM stack can't detect, govern, or revoke.
“Through 2028, over 50% of AI initiatives will halt, becoming unmanageable, because of unresolved agentic identity challenges.”
— Gartner, Tech FutureSight: Enterprise AI Scaling Requires Solving Agentic Identity
Close the gap between identity and authorization
Cerbos adds contextual, continuous authorization to your existing IAM ecosystem - centralized control, real-time visibility, and instant revocability for every identity type.
Cerbos externalizes authorization logic from application code, making access control consistent and centrally managed across all your services. Your IdP authenticates and assigns roles. Cerbos evaluates fine-grained access decisions at runtime - per request, per resource, per action. Aligned to NIST SP 800-207 Zero Trust architecture.
How Utility Warehouse achieved full control and compliance across thousands of services and millions of NHIs with Cerbos.
SOC 2 & ISO audit-ready
AI agents secured
Threat detection
“We can trace every permission, investigate suspicious behavior, and answer questions about who did what, when, and why. We’ve gone from guesswork to forensic-level auditing across humans, machines, and everything in between.”


Rob Crowe
Principal Engineer, Utility Warehouse
How Cerbos works
Your identity provider authenticates, Cerbos authorizes. Every decision is evaluated at runtime and logged for governance.
Seamless integration
Authorization that fits your stack
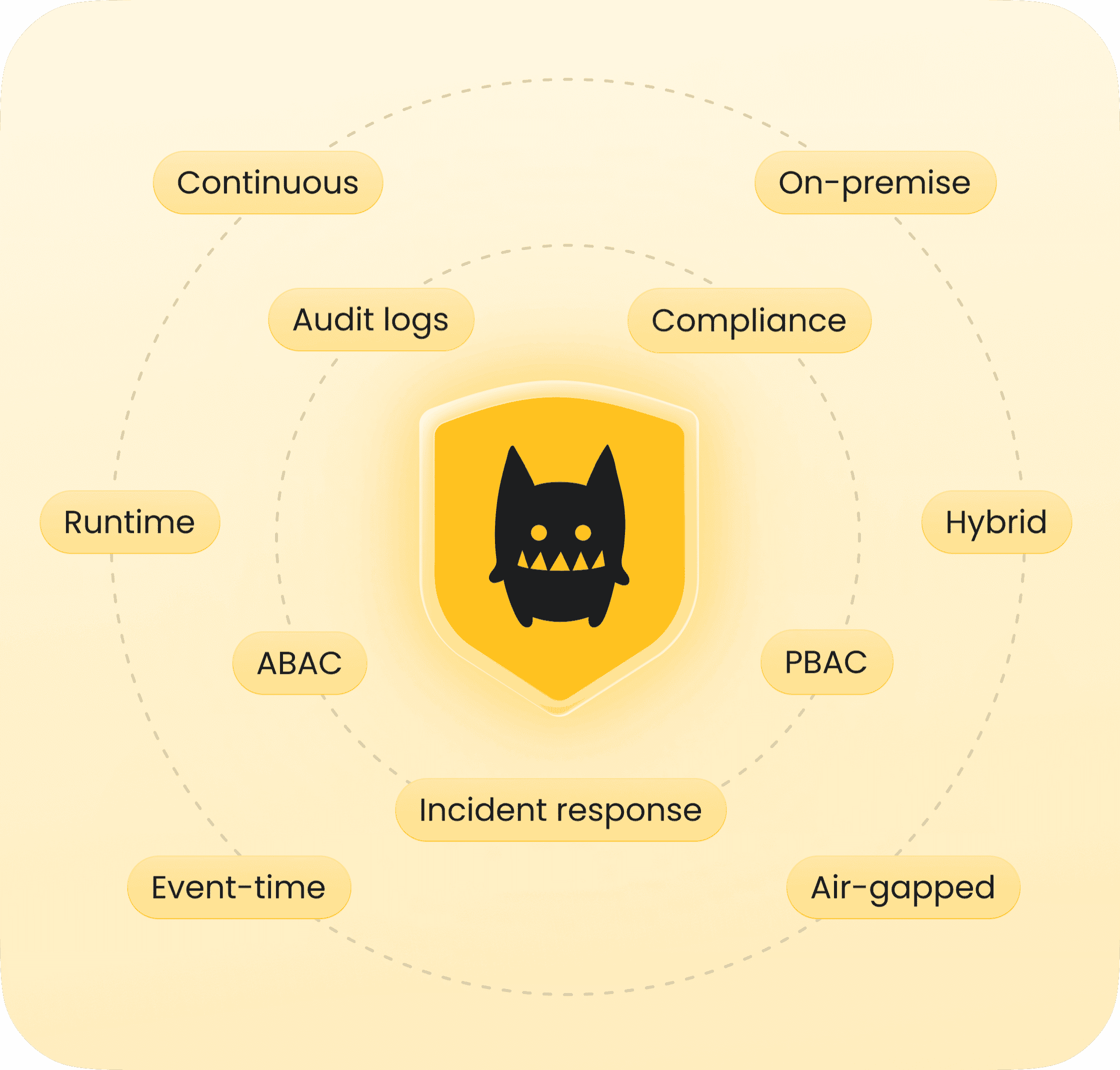
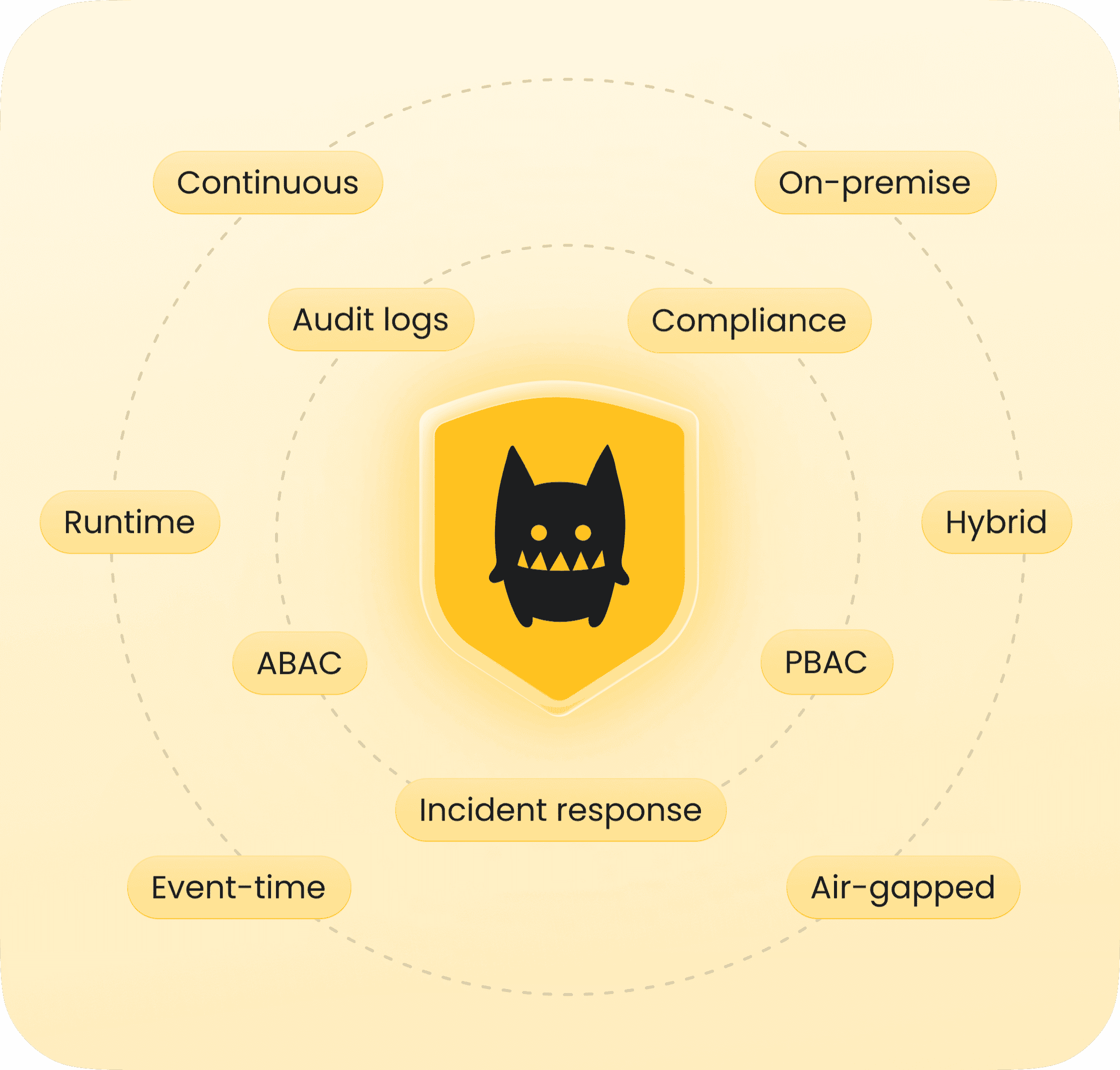
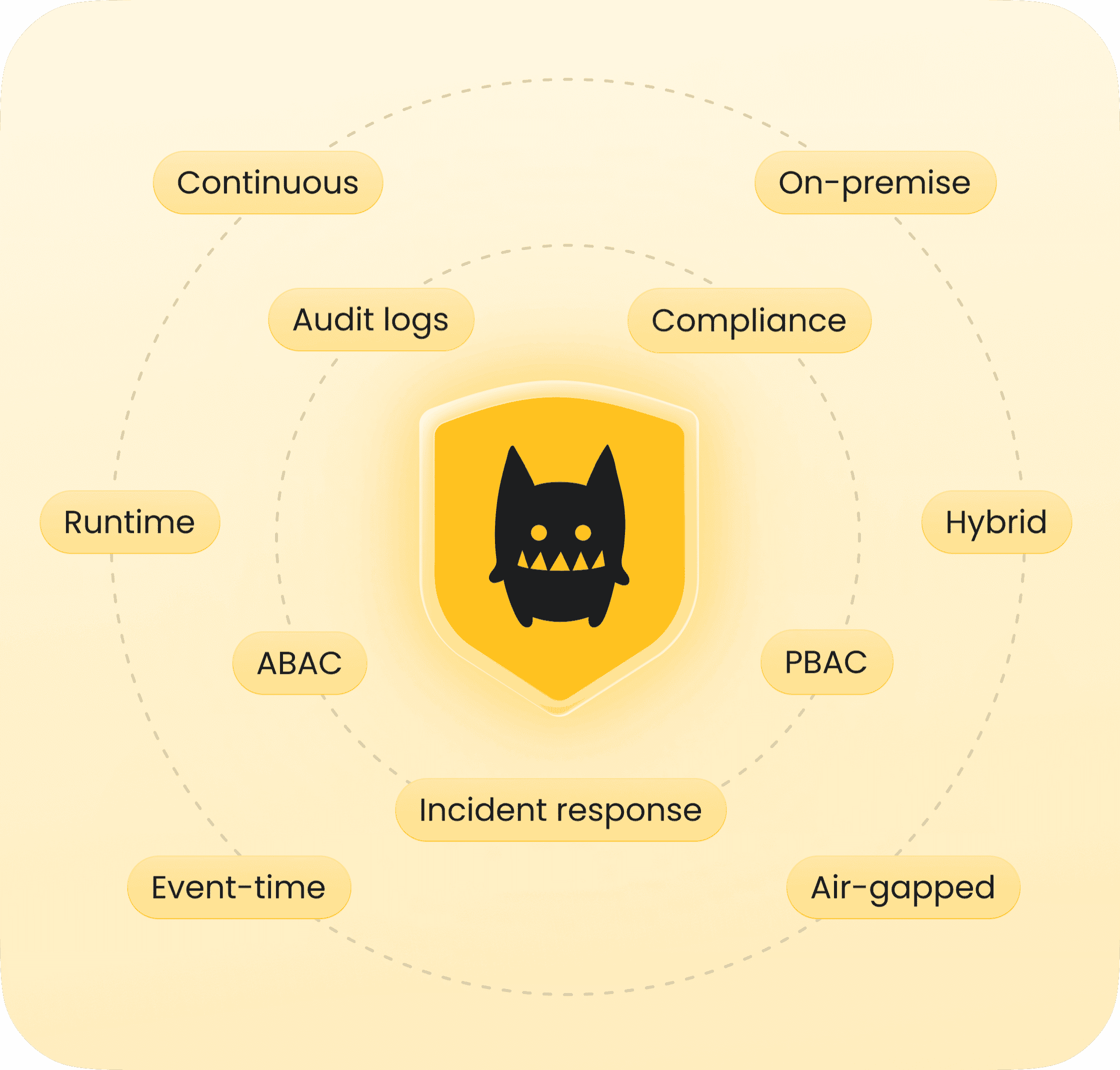
Access control for every use case
AI authorization
Enterprise authorization
ABAC
RBAC
ReBAC
PBAC
Runtime
Event-time
Admin-time
Audit-time
Cloud
Self-hosted
On-premise
Air-gapped
Compliance-ready with every decision
SOC 2 & 3
ISO 27001
PCI DSS

GDPR

HIPAA
FedRAMP
NIS2
DORA
Learn more about ZTA, identity governance, AI security, and compliance
Ebook
How to adopt externalized authorization
Article
Authorization became the main character at Gartner IAM
Article
Overcoming IAM blind spots and fragmentation

Article
CISO and architect’s guide to securing the new AI perimeter
Article
Zero trust has reached operational reality

Guide
Learning Zero Trust from aviation - the Swiss Cheese model

Guide
Framework for evaluating authorization solutions

Article
CISOs, identity failures and the road to continuous governance
Ready to control what your identities can do?
Cerbos gives your identity stack the missing piece - runtime authorization that lets you enable AI securely, see what every identity can access, and change it in seconds.
