If your authorization logic is scattered across a dozen codebases and you can't answer "who can access what?" in under a minute, that's not a technical gap. That's a career risk.
Authorization has quietly become the most consequential infrastructure decision security leaders face in 2026. Not authentication. Not identity governance. Authorization - the runtime control that decides, millisecond by millisecond, whether a request should be allowed or denied.
And increasingly, the organizations with the strictest security requirements are choosing to bring that control in-house with on-premise authorization platforms. Not because cloud is bad. Because when the board asks who had access to what and why, "our vendor's cloud handled it" isn't an answer that protects anyone's job.
The authorization problem nobody can afford to ignore
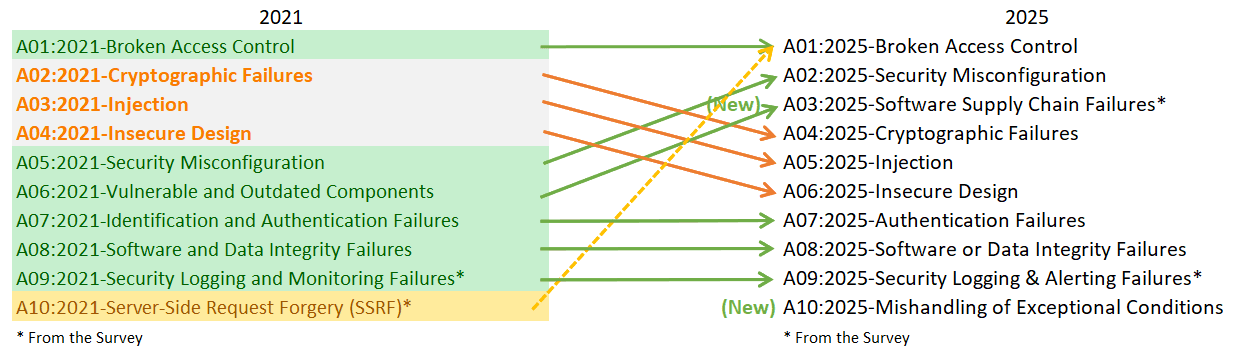
Broken access control has held the #1 spot on the OWASP Top 10 since 2021 and maintained it in 2025, with 100% of tested applications showing some form of access control vulnerability. It carries the highest number of associated CWEs of any category on the list. This isn't a niche technical issue - it's the most exploitable flaw in modern software.
Meanwhile, stolen credentials remain one of the most persistent breach vectors. Over the past decade, the use of stolen credentials has appeared in nearly one-third (31%) of all breaches, according to the Verizon 2024 Data Breach Investigations Report. That's not a new problem - but it's one that poor access control makes exponentially worse.
For security leaders, the implications are personal. The SEC's cybersecurity disclosure rules require public companies to report material breaches within four business days. Regulatory bodies across the U.S., EU, and beyond are expanding their focus beyond the enterprise to target named executives. The SolarWinds case - where the SEC brought charges directly against the CISO - signaled a shift that every security executive felt. While that specific case was eventually settled and dismissed, the precedent it set remains: CISOs can face personal liability for inadequate controls and incomplete disclosure.
The former Uber CISO's criminal conviction for concealing a breach made the stakes even clearer. Whether it's failing to report an incident or misrepresenting security posture, security leaders can be held personally accountable.
The financial data backs up the urgency. IBM's 2025 Cost of a Data Breach Report found that the global average breach cost sits at $4.44 million, while U.S. organizations face a record $10.22 million average. Among organizations that experienced an AI-related breach, 97% lacked proper access controls. That single statistic should give every CISO pause.
Why authorization is now a board-level conversation
Across the industry - from conversations with security teams at regulated enterprises to sessions at events like Gartner IAM, Identiverse, and EIC - we're seeing authorization move from a background concern to a board-level priority. It's no longer tucked inside access management as a checkbox feature. Industry analysts now recognize Authorization Management Platforms (AMPs) as their own tool category, sitting alongside IGA, PAM, and ITDR in the IAM stack. That's a meaningful shift.
The reason is straightforward: neither identity governance nor traditional access management delivers fine-grained, dynamic, real-time authorization. IGA handles static roles and groups. Access management gives you coarse-grained controls. Neither can make the kind of context-aware, attribute-driven decisions that modern architectures demand.
The AI dimension accelerates everything. Gartner predicts that 40% of enterprise applications will integrate task-specific AI agents by the end of 2026, up from less than 5% in 2025. Boards have signed off on agent strategies, announced them to stakeholders, set timelines. And the job of actually securing these agents has landed squarely on identity and security teams.
From working with dozens of security teams navigating this shift, we keep hearing the same story: the board has bought into AI, budget is flowing, agents are being built or bought - and the security team found out somewhere between "proof of concept" and "we're going live next month." The authorization requirements for AI agents are fundamentally different from traditional applications: fine-grained access control, context-aware decisions, delegation of authority, human-in-the-loop flows, rich authorization requests, and session-aware evaluation. Every single one of these points toward policy-based, attribute-driven authorization rather than static role assignments.
IBM's research supports this concern: one in five organizations reported breaches due to shadow AI - unsanctioned AI tools adopted by employees without IT oversight - adding an average of $670,000 in extra breach costs. Among those breaches, 97% of organizations lacked proper AI access controls, and 63% had no AI governance policies in place at all.
The message from every direction is clear: the board bought AI, and the identity team got the bill.
The case for on-premise authorization
So if authorization is critical infrastructure, why are enterprises choosing on-premise authorization over cloud-hosted alternatives? The answer comes down to the questions security leaders actually need to answer when something goes wrong.
Data sovereignty and residency
For organizations operating in regulated industries - finance, healthcare, insurance, government, defense - authorization decisions and audit logs contain some of the most sensitive operational data in the stack. Every decision captures who requested access, to what resource, under what policy, and what the outcome was. Sending that data to a third-party cloud, even an encrypted one, introduces compliance risk that many regulators won't accept.
On-prem authorization keeps policies, decision logs, and audit trails within your controlled infrastructure. That matters for GDPR (where fines have exceeded €6.7 billion as of January 2026), DORA, NIS2, HIPAA, PCI DSS, and sector-specific regulations that mandate data residency.
Air-gapped and connectivity-constrained environments
Government agencies, defense contractors, and critical infrastructure operators often run environments that can't connect to external services at all. Authorization decisions happen at runtime - every API call, every resource access, every agent action. If your authorization engine requires a cloud connection to function, a network disruption becomes an authorization outage, and an authorization outage becomes a security incident.
Self-hosted authorization running in your data center, your private cloud, or a fully air-gapped network means authorization decisions continue regardless of external connectivity.
Incident response speed
When a breach happens, the clock starts immediately. You need to answer "what could this account access?" and "which policy allowed it?" within minutes, not days. IBM's research shows that organizations using AI and automation extensively reduced their breach lifecycle by an average of 80 days and saved nearly $1.9 million. Speed of detection and containment is the single biggest factor in reducing breach costs.
With on-premise authorization and centralized audit logging, your incident response team can trace every access decision back to the exact policy version, the context that was evaluated, and the outcome - without filing a support ticket with a vendor or waiting for data exports.
Full control over the authorization stack
Over-provisioning is rampant across enterprise environments. From conversations with security teams and industry research, the pattern is consistent: the vast majority of identities use only a fraction of their granted entitlements. The tooling to detect and correct this needs to sit where the decisions happen.
With an on-premise authorization platform, security teams control the entire policy lifecycle: authoring, testing, deployment, evaluation, and auditing. There's no dependency on an external service's availability, no questions about where your policy data lives, and no gaps between what you define and what gets enforced.
What to look for in an on-premise authorization solution
Not every authorization tool is built for on-premise deployment, and "self-hosted" shouldn't mean "limited." Here's what matters:
Policy-as-code. Authorization policies should be version-controlled in Git, testable in CI/CD pipelines, and reviewable by both security and engineering teams. This isn't a future aspiration - it's a current requirement for any organization that wants authorization to be auditable, repeatable, and defensible.
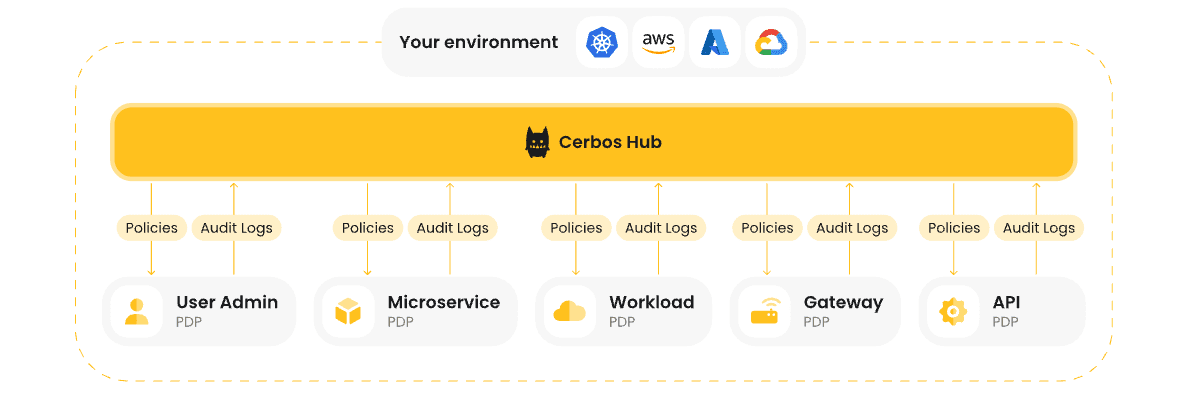
Centralized policy administration with decentralized enforcement. This is the canonical architecture the industry is converging on: a Policy Administration Point (PAP) manages policies centrally, while Policy Decision Points (PDPs) run wherever enforcement needs to happen - in front of APIs, inside services, between agents and their tools. This pattern ensures consistency without creating bottlenecks.
Standards-based interoperability. AuthZEN - the OpenID standard for PDP-to-PEP communication - is emerging as the connective tissue between authorization engines and enforcement points. It showed up across multiple analyst sessions at recent industry events, with independent researchers pointing to the same standard. Solutions that support AuthZEN and other open standards avoid vendor lock-in and enable composable identity architectures.

Deterministic, real-time decisions. This is a point that industry analysts have been clear about: authorization is not fit for AI-based decision-making because it requires deterministic results at millisecond latency. AI belongs upstream - analyzing access patterns, modeling better policies, finding over-provisioning. The runtime decision itself must be deterministic every time.
Full deployment flexibility. On-prem data centers, bring-your-own-cloud, air-gapped networks, and hybrid architectures should all be first-class deployment targets - not afterthoughts.
Not every organization needs on-prem, but every organization needs options
It's worth being honest about something: self-hosted authorization isn't the right fit for every situation.
For organizations without strict data residency requirements, cloud-hosted authorization can be faster to deploy, easier to maintain, and operationally simpler. Startups, early-stage SaaS companies, and teams without dedicated infrastructure operations may find cloud-hosted platforms give them the authorization capabilities they need without the overhead of managing the deployment themselves.
The organizations that genuinely need on-premise tend to share specific characteristics: regulatory mandates around data sovereignty, air-gapped or connectivity-constrained environments, government or defense contracts requiring infrastructure isolation, or internal security policies that prohibit sensitive operational data from leaving the perimeter.
The important thing is having the choice. Your authorization platform shouldn't force a deployment model on you. As your security posture evolves, as you enter new markets, as regulations change - you need the flexibility to move between cloud-hosted, self-hosted, hybrid, and air-gapped without re-architecting your entire authorization stack.
How Cerbos fits
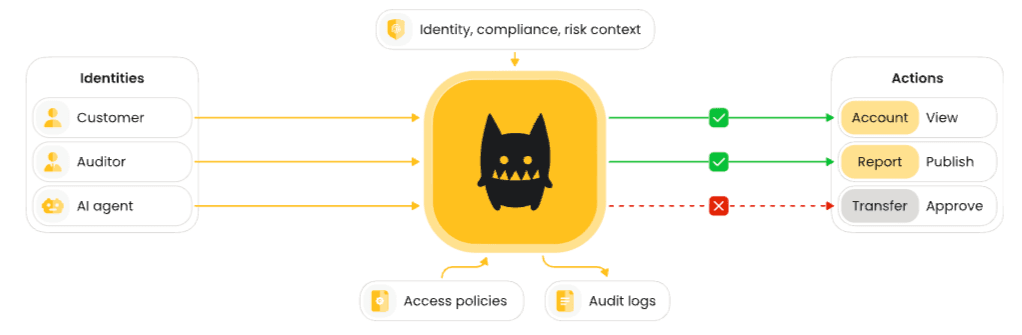
Cerbos is an enterprise-grade authorization software built to secure access across complex, distributed environments, SaaS products, and regulated systems. It externalizes authorization logic from application code, making access control consistent and centrally managed across all your services.
Designed for Zero Trust architectures and AI-driven systems, Cerbos provides continuous, policy-based authorization that scales from local deployments to global production systems. It supports multiple access control models - RBAC, ABAC, and PBAC - giving engineering and security teams the flexibility to model permissions the way their business needs them.
Cerbos' authorization system consists of three connected components working as one platform:
The Policy Decision Point (PDP) is the open-source authorization engine that evaluates access control logic and returns allow or deny decisions. It's stateless and lightweight, running anywhere - in containers, Kubernetes clusters, or at the edge - and is optimized to handle millions of authorization checks per second with predictable latency.
Enforcement Point SDKs are lightweight libraries that enforce authorization decisions directly within your applications and APIs, providing a simple, language-agnostic interface for calling the PDP in real time.
Cerbos Hub is the Policy Administration Point - authorization management software for authoring, testing, deploying, and auditing authorization policies at scale.
Cerbos Synapse is the latest component that completes the platform. It gathers identity, resource, and relationship data from your existing systems - identity providers, databases, graph databases, internal APIs - and delivers complete context to the policy engine before every authorization decision.
Together, these four components give enterprise teams a single governed layer for every authorization decision.
With the release of on-premise Cerbos Hub, the full platform runs entirely inside your environment. No cloud dependency. No data leaving your perimeter. But if cloud-hosted works better for your organization, that option is equally supported. So are hybrid architectures. Cerbos gives you all deployment models - on-prem data centers, bring-your-own-cloud, fully air-gapped networks, and cloud-hosted - so you're never locked into a single approach.
Cerbos handles authorization across the full scope of what modern enterprises need to secure: AI agents and MCP servers, RAG pipeline filtering, multi-tenant SaaS, non-human identities, and agentic systems. It enforces least privilege at scale and maintains full visibility into every access decision with detailed audit logs. The Cerbos PDP already supports the AuthZEN standard, and the platform is compliance-ready for SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR, and FedRAMP.
The real question
Building authorization yourself is one of the most common patterns we see - and one of the hardest to defend when something goes wrong. The risks are well-documented: development costs, exploitable bugs, regulatory difficulty, no community support, and longer time to market. Homegrown authorization logic that nobody wants to maintain is the situation security architects describe most often.
The question isn't whether you need to modernize authorization. It's whether the approach you choose will hold up under scrutiny.
Every vendor decision a CISO makes ultimately answers one question: "If this goes wrong, can I defend this decision to my CEO and board?" An enterprise authorization platform with centralized policies, deterministic decisions, full audit trails, and deployment flexibility - whether on-prem, cloud, or hybrid - is about the most defensible answer there is.
The organizations building this authorization layer now will ship AI agents faster, pass audits with less friction, and respond to incidents with clarity rather than chaos. The ones that don't will find themselves stalled - unable to move AI initiatives into production because they couldn't solve authorization.
Your authorization infrastructure is either an asset that protects you or a liability that exposes you. There's not much middle ground left.
Ready to see how enterprise authorization works in practice? Talk to the Cerbos team or explore on-premise Cerbos Hub to understand how it fits your environment.
FAQ
Tagged in