Govern Claude Code agents with centralized authorization policies
Enforce role-based tool access, block sensitive file reads, and audit every agent action across your organization with Cerbos Synapse and Cerbos Hub.
Tool-level access control
Control which tools each role can invoke. Engineers get full access, non-technical teams get read-only, with fine-grained command-level restrictions for everyone.
External enforcement point
Policies are evaluated outside the agent process by Cerbos Synapse. The agent cannot override, skip, or reinterpret authorization decisions.
Org-wide audit trail
Every allow and deny decision streams to Cerbos Hub with full context, giving you a searchable, tamper-resistant record of all agent activity.
How Cerbos works with Claude Code
AI agents and tools introduce a new class of authorization challenges. They act on behalf of users, access sensitive data, and chain operations, all of which need fine-grained access control.
Cerbos provides policy-driven authorization that controls what AI systems can do, which data they can access, and on whose behalf. Policies are written in human-readable YAML and evaluated at request time.
With Cerbos and Claude Code, you get guardrails that scale with your AI adoption, centrally managed policies, full audit trails, and sub-millisecond decision times that don't slow down agent workflows.
How Cerbos governs Claude Code
Claude Code has an HTTP hooks system that sends every tool call to an external service for approval before it executes. Cerbos Synapse sits at that endpoint, evaluates the request against your authorization policies, and returns allow or deny.
The enforcement point lives outside the agent's process. The agent cannot modify the policy, skip the check, or "make assumptions" about its permissions.
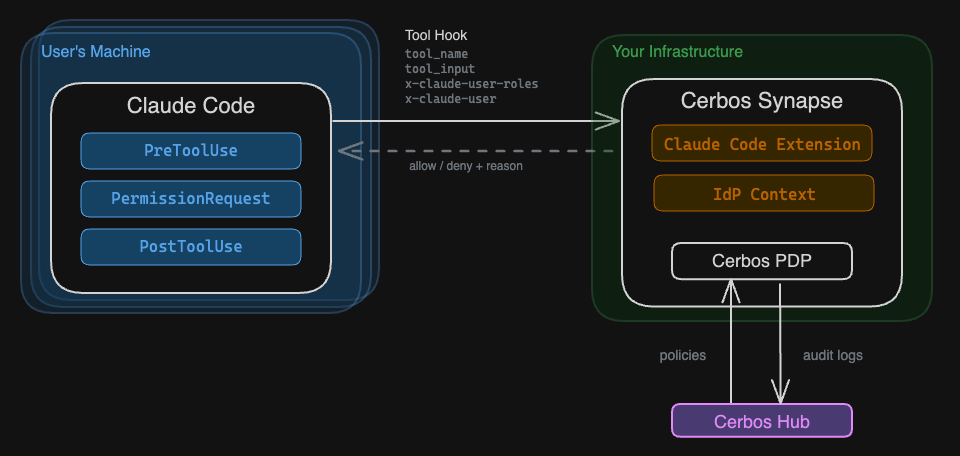
Synapse's built-in extension converts Claude Code hook payloads into standard Cerbos authorization checks:
- Hook event (PreToolUse, PostToolUse) becomes the resource kind
- Tool name (Bash, Read, Write) becomes the action
- User headers become the principal (identity and roles)
- Full hook payload lands in resource attributes for fine-grained conditions
Org-wide enforcement with server-managed settings
Claude Code supports server-managed settings pushed via MDM (Jamf, Intune). These settings cannot be overridden locally, so every developer's agent is governed by the same policies. No opt-outs, no forgotten configs.
Example: protect sensitive files for all roles
apiVersion: api.cerbos.dev/v1
resourcePolicy:
resource: PreToolUse
version: default
rules:
- actions: ["Read", "Write", "Edit"]
effect: EFFECT_DENY
roles: ["*"]
condition:
match:
any:
of:
- expr: R.attr.tool_input.file_path.matches(".*\\.env.*")
- expr: R.attr.tool_input.file_path.matches(".*secret.*")
- expr: R.attr.tool_input.file_path.matches(".*credentials.*")
Example: role-based tool access
- actions: ["Bash"]
effect: EFFECT_ALLOW
roles: ["engineer"]
- actions: ["Bash", "Write", "Edit"]
effect: EFFECT_DENY
roles: ["marketing"]
Start in observe mode
Deploy Synapse with no policies. Everything gets allowed, but every tool call is logged. See what your agents actually do across the org, then write policies based on real data.
FAQ
How does Cerbos govern Claude Code agents?
Cerbos Synapse intercepts every Claude Code tool call via HTTP hooks. Each tool invocation (Bash, Read, Write, Edit) is checked against centrally managed Cerbos policies before it executes. The agent never sees or controls the policy. Decisions are logged to Cerbos Hub for audit and compliance.
Can I restrict tool access based on team or role?
Yes. Claude Code hook headers carry the user's identity and roles to Synapse. Cerbos policies can grant engineers full access while limiting marketing or product teams to read-only tools. Roles are set through server-managed settings pushed via MDM, so users cannot override them.
Can I block specific commands even for trusted roles?
Yes. Cerbos policies can inspect the full tool payload, including Bash command strings and file paths. You can block destructive commands like rm -rf, git push --force, and curl-pipe-bash for all roles while still allowing safe Bash usage.
Does this add latency to Claude Code?
No. Cerbos Synapse runs as a lightweight local or network service and delivers sub-millisecond authorization decisions. Tool authorization adds negligible overhead to agent execution.
Can I start without enforcing any restrictions?
Yes. Deploy Synapse in observe mode with no policies defined. Everything gets allowed, but every tool call is logged to Cerbos Hub. Run it for a week to see what your agents actually do, then write policies based on real data.
Learn more about Cerbos
Related integrations
View all integrations →Cerbos + Claude Code
- Cerbos policies govern AI agent tool access and data visibility
- Full audit trail for every AI tool call and data access
- Per-user permissions enforced across autonomous agent workflows
- Sub-millisecond policy evaluation with no agent pipeline overhead